Computer Star
Computer Repair, Laptop Service, Mac repair, Data Recovery Ridgeway Drive Mississauga
For expert Apple Macbook repair, laptop repair, PC computer desktop help and all Apple products services, please call us at 905-272-8324
Basic Free Computer Laptop Troubleshooting instructions.
On AC but not charging
Steps to fix this laptop battery problem:
1.Shutdown your laptop
2.unplug the power cord
3. Remove the battery
4. Turn on the laptop
5. Shut down the laptop
6. Install the battery in the laptop
7. Plug in the ac power adapter
8. Turn on the laptop
9. Go to device manager
Open batteries tab- delete ACPI compliance control method battery. Then "scan for new hardware" from action menu.
XP anti-virus 2011 removal instructions
Here is how to remove xp anti-virus 2011.
Open windows explorer. Click on tools-folder options. Click on view tab. Under "hide files and folders" unhide files and folders. Unhide protected operating system files. Run an off-line antivirus scan. Run malwarebytes scan. Hope this works. This method also apply to XP home security(It's also called XP home security - unregistered version), XP Internet Security 2011 firewall (process in task manager xwt.exe), Vista antispyware 2012 firewall alert ( process otl.exe), Win 7 security 2012 alert & MS Removal tool threats. This threat runs with the help of cli.exe process.
Windows cannot be installed to Disk 0 Partition 1. (Show details)
This process also works if you want to convert dynamic disk to normal disk.
Boot your disk with windows 7 or vista. Instead of installing windows select "repair windows". Select the first option. Click on dos prompt. on the dos window type "diskpart" and press enter. Type "list disk". All the disks will be displayed. Type "select disk 0 or 1 (look for disk number). Type "det disk" and enter to see all partitions. Type "clean all" (this will delete all partitions and data) and press enter. Exit by typing "exit" and enter. Close the DOS windows and refresh to see the disk again. Install Windows 7 or vista.
"Community toolbar" error message at Mac startup
Steps how to remove this message when you startup or login to your iMac or MacBook. Go to finder. Then click on applications. Go to the related toolbar folder. Double click on uninstall. Enter the username and password and that's it (this error message has nothing to do with startup items).
This computer's hardware may not support booting to this disk
If you have a computer that has an un-initialized disk, This message will popup during Windows Vista installation. To fix this problem, create partitions on your hard drive during vista installation stage. After partitioning your hard drive, restart your computer and start the Windows installing again.
Which antivirus is good?
There are a few reputable antivirus companies that are experienced. Some of those are Symantec (popular as Norton), Trend Micro, Zone Alarm, McAfee, Kaspersky, Microsoft Security Essentials, Avast, AVG, Panda, and others. There is no good or bad but those with more years in this business are considered better. It is always recommended to keep the operation system and antivirus up to date.
Computers and Laptops
In this article I will talk about computers and laptops. Computers and laptops are actively being used in the market by people of all walks of lives. I explained about different functions and types of computers too.
A computer usually means desktop machine with a CPU box (also called PC), a monitor, keyboard and a mouse. Two companies manufacture them. Apple makes Mac, MacBook, iMac, while Microsoft is linked to PCs. The computer comes pre-loaded with an operating system. Mostly it comes with Windows operating system. Different operating systems can be installed on the machine. One of them is the Unix and Linex. Google operating system is also an option but it did not get famous due to lake of interest. A computer can be used in homes and offices. It can be used for running machines and different equipment for automated functions. A computer can be used for different operations. A common user uses it for reading newspaper, facbook, youtube, typing, printing or listing music. There are so many uses of a computer also known as PC (Personal Computer). In business, there are numerous uses of personal computers.
Computers are built for non stop use (day and night). They have the ability to stay awake or can go to sleep after long inactivity. They get a little sluggish if turned on for a long time. Restarting a computer once in a while can improve its performance. If a desktop computer stays on for days and there is some electricity issues at any given time this can cause electrical problems making them unusable. To overcome such issues, uninterrupted power supply can be used. This device also known as UPS, runs with the help of batteries, can save it from dying as a result of bad lighting storm. In such situation, where there is a power loss, different components inside the PC can go bad. This includes power supply, motherboard, RAM and hard drive. Hard drive failure is the most common among all problems.
When a hard drive goes bad in a PC, this is an indication of a big problem. People store documents, photos, videos, music, office files, business data, employee information, databases and programs on computers. The hard drive stores all this material. A hard drive failure could be software related or hardware oriented. The hardware issue is mostly complicated. A data recovery company can recover data from the broken hard drive. Computers are also famous for getting viruses especially Windows operating system. Normally a virus can be removed to make the computer usable but some viruses are programmed to make irreversible damage. These programs encrypt user data which is impossible to recover. Most of the facts mentioned above apply to laptops.
Laptops are compact form of personal computers. The screen is built-in. The keyboard and trackpad is also built-in. The laptops are great computers for mobile use. They have disadvantages too. They need proper ventilation for heat otherwise they heat up and go bad. Laptops depend on batteries when there is no electricity but the good thing about them is, they can be used worldwide when it comes to electricity requirements. The most common issues in laptops are heat, battery, liquid damage and physical damage. They are great machines overall. Laptops use 2.5 inch hard drive compare to desktop computers which use 3.5 inch drives. Processors are mostly built-in in laptops, while in desktops they are removable.
In this article, I explained a few facts about the daily used popular machines known as computers and laptops. I tried to show some basic facts about laptops and desktop computers.
How to be a computer technician
In this article I would discuss different ways to be a computer technician. There are different kinds of computer technicians. A PC technician, Mac technician and data recovery technician. A PC technician is the one who is trained for PC or laptop repair. This repair could be a software or hardware repair. A software repair includes fixing operating system or application related problems. A hardware repair is mainly related to parts in the PC or laptop. There is no limit on how much computer education the person should have. On the lower side if he has a computer technician diploma then he can start work as computer technician. Usually A+ certification (This course includes Microsoft and other related certifications) is the official certificate that is required by most of employer when they look for computer techs. In most cases a grade 10 plus a computer diploma or a plus certification is enough.
Other kind of technician is a Mac technician. Let me differentiate between two plate forms that are mainly used these days. One is Windows and the other one is Macintosh. Microsoft makes windows and Apple develops Mac. All the operating systems developed by Microsoft (Windows 3.1, Windows 95, Windows 98, Windows Minimum, Windows 2000, Windows XP, Windows vista and Windows 7) are called windows plate forms. On the other side, Panther, Tiger, Leopard and snow leopard are the operating systems written by Apple engineers. Apple operating system only works at their own hardware that means Apple make their own computer machines to be used with their plate form. Windows operating system runs on PC (personal computer), laptop or netbook. There are other platforms that are very rarely used like UNIX and Linux. To become a Mac technician, one must be an Apple certified. Obviously experience is required after certification.
It’s a trend that a PC technician would not work on Mac machine. The reason in my opinion is Mac machines are more delicate and sensitive when it comes to repair them. The software platform is totally different than Windows system. The other reason could be the cost of these machines. Mac computers are expensive and personal computer technicians do not want to take risk. Another reason is parts for Mac computers are not available everywhere like PC parts are.
The next kind of computer technician is data recovery tech. This is the most high tech job. There are two important steps to become a computer data recovery specialist. First, one must have expert knowledge of storage media e.g. opening a hard drives and must be trained to understand how hard disk or data storages work. A data recovery course or hard disk repair course is must for data recovery technicians. Data recovery job involves using different type of equipment. A Hard disk expert is trained on how to these data recovery equipments. Data recovery expert must use this kind of technology. The recovery process is not simple to follow especially using these machines. Whether it is PC, Mac or data recovery technician, one must be certified and experienced to do the job properly.
This article explains how many types of technicians are out there and requirements to become a personal computer, Mac or data recovery technician.
Tags: Data recovery technician, PC technician, Mac technician, how to become a computer technician, PC technician.
Lenovo T410 screen replacement
If your laptop screen is broken, it can be repaired. All you need is an led screen to replace. I will explain step-by-step instructions here. First of all remove the rubber cover from screws on both lower corner of the screen. There are two screws in pair on both sides. Then use a flat (thin) screwdriver to remove the top cover of the LCD screen. After that you have to open the top single screws on both upper corners. Now you can pull out the screen and remove the led cable from the back of the screen. Now remove the two metal brackets on both side of the LCD. Take the new screen and attach these brackets to it. Install the new screen the same way the old and finish everything properly. It won’t take more than 15 minutes.
How to save a screen shot
You can save any screen using word pad or ms word. Select any thing like a web page in Internet explorer, desktop or email page and click on the key "print screen" or prt or sysrq on your keyboard. Then open notepad or Microsoft Word, works or iWorks (if you are using Mac). Open a blank page and click on edit and then left click on paste. You will see whatever was on the screen will appear in your application. Click on file and then save as to save the screen shot by giving it a name.
Mac OS X upgrade / Archive and install
Sometimes if operating system is slow or has minor problems, users would perform an upgrade or archive & install. The other situation would be to upgrade from let say Tiger to leopard or snow leopard. It's very important to understand that this kind of action can destroy the data. In this kind of situation, you must know what steps to follow because you may notice missing files or data. If you have done it and cannot find your files, photos or documents, the data can still be recovered. Only advanced users or computer professionals can save your data. The same applies to Windows (from XP to vista or Windows 7 or repair install) and PCs.
Mouse right click does not work in Windows 7 installed on MacBook Pro
After you install Windows 7 home premium or other version on a MacBook Pro, right click on track pad might not work. You need to go to control panel and open boot camp program. Click on track pad tab in the small window. Then check the check box (last one) to enable right click as secondary function.
How to take ownership of a folder in Mac
When you double click on a folder, you get an error message "could not be opened because you do not have sufficient access privileges"
If you have copied data from one machine or hard drive to another or recovered data, you might not be able to access contents of a folder. Such folder will display a red minus sign on top of it. Right click on the folder or drive and click on "get info". In the bottom of the new window, you will see "sharing and permissions". Click on the lock beside it on the right side and enter your user name and password. The lock will open which means you now can take ownership of the folder or drive. So click on "everyone" under "share and permission" and to the right of it, you will see "no access". Beside "no access you will see two small arrows pointing up and down, click on it and change it to "read & write. You will now have full access to the target folder or partition.
Hide check box gray out
If a virus has changed hidden attributes, it can be fixed. You right click on a file or folder and you find that the hidden check box is grayed out, which means you cannot uncheck it. For this reason you only see your files or folder in fade color if you unhide files and folders through tools and folder options. To fix this problem in windows XP, click on "start" then click "run" type "cmd" a black window will open. On the command prompt type the drive letter (for example d:)you want to go to. Now type attrib -s -h *.* /s /d
This will get rid of the grayed checkbox beside the hidden attribute.
The volume has the wrong case sensitivity for a backup
This is the message that you will get when you try to copy time machine backup from one hard drive to another. I checked instructions on Apple website but those instructions do not work or these instructions are incomplete. Here is the solution to this message "The volume has the wrong case sensitivity for a backup".
1. Connect the target drive to a machine that has OSX lion on it. Go to disk utility and format the drive using Mac OSX extended (journaled). Also make sure you chose the option of "Guide partition".
2. Enter in Time machine and select this drive for backup. Then turn off the time machine by sliding the bar to "off" position.
3. Now copy your files from the source hard drive to the target one and you are done.
These instructions seems easy but it won't work on OSX 10.6 or lower. There are so many kinds of messages and situations where it is hard to copy time machine backup folder when dealing with different version of Mac OSX but every situation should be handled differently.
Internet Security virus removal process
I found this virus on a windows 8 laptop. It does not allow opening any program. As soon as the computer user opens a program, it displays an alert in the right lower corner of the screen. You will need to go to safe mode to remove it. How you go to safe mode in Windows 8? You have to stop the internet security virus process but you can't because as soon as you try to open task manager, it stops you. All you have to do is to stop the program by right click in the startup items at the right lower corner of the screen and click on settings and uncheck "start at windows startup" and reboot. You can also stop it by closing it with red x. Then the PC will allow you to go to task manager and stop all harmful processes. Then open "msconfig" and select "boot" and then choose safe boot. Restart the computer in safe mode and rename the program which may be hiding in roaming folder under user account. After that restart the computer in normal mode and run malwarebytes to get rid of the remaining malware.
Mac Desktop Computers and MacBooks
In this article, I will share my knowledge about Apple’s Mac desktop computers and MacBooks. Apple started its Mac computer manufacturing in 80’s but for reasons or the other, the company could not impress the consumer market. Microsoft operating system ruled the globe for several decades until a times arrived which diverted computer users from PC computers to Mac computers. Initially Apple computers were manufactured with IBM processor which was one of the reasons why Mac computer were not popular because all PC computers were using Intel chipsets and all programs were being written for Intel based computers and because Mac computers were G based, it was hard for software developers to make small changes to their programs to make it work with Mac machines. There is still a huge market that is dominated by personal computers but Mac computers are getting more and more familiar. About 5 years back, I had no idea about the future of these Apple’s computers but now it is booming. Mac Computers are machines made by one and only one company known as Apple. All the hardware and software is the ownership of just one company. I don’t think, it’s good news for businesses.
When it comes to PCs, there so many companies involved in making hardware or mostly making computers and laptops. Anyways, coming back to topic, Mac computers are getting popular day by day. There are two big time reasons why these machines are getting popular. Number one is the software is better because a) it does not catch viruses very often b) it is more innovative. The second reason is the introduction of Intel based machines. Because most of the software or applications are Intel based. Apple felt it and took the right step to move to Intel chipset. Apart from these two reasons, apple hardware is a little better then a normal hardware. Apple has launched most of their best machines so far. In desktop, they have made two kinds so far, a tower and all in one iMac. In towers they mad small cubical CPUs called Mac mini. In laptops they made PowerBook G4, iBook, MacBook, MacBook Air. If I dig it further then they made two kinds of families of MacBooks, a unibody and a pre-unibody. Same way in desktop they had Power PCs with IBM chip and later on they came with Intel based machines. The operating system which usually called OSX, is also developed by Apple. Some of the most popular names of these operating systems are Panther, Tiger, Leopard, Snow Leopard and Lion. OSX, Lion is the latest operating system in today’s date. There are usually two kinds of drawbacks when it comes to Mac computers and laptops. One is not every application or software is compatible with Mac operating systems. As time goes on, more and more applications are being developed for Mac computers. In the beginning it was a huge problem because most of software was not compatible. This trend has changed dramatically over the past few years. Second, these machines are pricey compare to PCs and PC laptops. Mac users justify it by saying that the cost over time is not that much which make it sounds better.
In this article I have explained in detail about Apple’s family of Mac computers, operating systems, advantages and disadvantages.
If you need help with your Macbook or MacBook, pl. visit our MacBook Repair page.
Apple iPad, Macbook, Mac Pro, iPhone
Mac computers were being manufactured in 80’s but for some strange reasons, people were not impressed most probably another company was doing well in computer area. Windows operating system was making its way to dominate the world for several decades until virus era arrived, which forced computer users from PC to Apple’s Mac computers. Apple computers were using IBM processor in the beginning, which hold it away from huge consumers market for a while. The main reason was PC computers were using Intel chipsets and software manufacturers were developing software for Intel based computers and because Mac computers were IBM chipset, it was not feasible for computer users.
At the moment about 70-75 percent of the world market is being dominated by Microsoft based windows computers but Apple’s computers which are known as Mac computers are growing its market share. A few years back, one could not even imagine that Apple computers would be so popular. Apple is the only company in the world that makes Mac Computers. This means one company controls everything about Mac computers and laptops i.e. operating system and desktop and laptop computers which do not seem like a good idea for other businesses but in my opinion, this may be good as long as quality is concerned. The reason I am saying this is when we look at PCs and laptops, many different companies are involved in the business i.e. only one company make the operating system which is Windows and all others make hardware like laptops, desktops, parts and other hand held devices. Coming back to topic, Mac computers are slowly dominating the market share. How long and how far it will go, it’s too early to guess.
So what is the reason Apple computers are getting popular? In my opinion, there are two basic reasons. One is (a) better software architecture (b) Innovation. Second reason is very important. PCs and laptops computers are based on Intel based processors. So all software manufacturers always design software and applications for Intel based machines. Apple was using IBM processor (called G 3, G 4, G 5). When Apple realized that this area is hijacking their progress, they switched to Intel and got a big boost in popularity. There are some other reasons that make Apple computers different from a PC and that is the hardware layer is better than PCs. For example the battery life of Apple MacBooks, iPads, and iPhone, is very good. Some of their machines like iMac are more popular than a normal PC computer.
Apple line up of computers includes three types of machines. In desktops, they have iMac, towers and small factor. iMac is all in one machine. Only a mouse and keyboard is required to operate it. In tower, they have G towers and Intel towers and Mac Pros. They also have a compact machine called Mac mini. These are small factor machines but are powerful and innovative products. Mac mini is like a PC CPU that connects to a monitor, mouse and keyboard. The other lineup is the most popular one and that is their laptop product which includes PowerBook G4, iBook, MacBook Pro, MacBook Air. In MacBooks, they have older types like G based machines and newer kind that includes Intel based machines like pre-unibody MacBooks and Unibody MacBook Pros. Similarly, in desktops, they have computers with IBM processors and Intel chip. The third type of Apple products are hand held devices including iPad, iPhone and iPod.
Their operating system is called Mac OSX. This includes Panther, Tiger, Leopard, Snow Leopard, Lion and Mountain Lion. OSX, Mountain Lion is the latest operating system in today’s date. Mac machines are expensive than PCs. The reason is they are more innovative and are strong against viruses. Apple computers had big time issues with compatibility in the past but that is almost gone now. Most applications are now compatible with Mac computers. In the past, it was hard to find software and hardware that would work with Mac computers but not any more. Nowadays every hardware and software meets system requirements for Apple computers and MacBooks. All this happened very quickly in the last few years. In general Mac computers use the same storage devices that PC systems use which means hard drive or hardware failure is no different than PCs.
Types of computer and laptop drives
In this article I will talk about different types of hard drives including flash drives, SSD drives, external hard drives and internal drives.
The first one is USB flash drive. USB flash drives are basically same except the physical size of the device. Some comes in regular size other comes in flat shape. Some of them are micro USB. Physical data recovery from Micro USB is not possible because of the small chip size. USB best drives are very popular right now. The reason is the size and portability. Files can easily be transported from one computer to another. USB flash drives comes in only one file format thus these can be used in PC and Mac computers. These drives come with a FAT file system. Flash drives also called thumb drives comes in different capacities starting from 32mb to 64GB. USB drives are safe devices unlike traditional hard drives whose failure rate is much higher than USB drives. The reason is these flash drives do not use heads and platters. Thumb drives use flash memory for data storage.
The next type of storage media is the famous hard drive. Hard drives come in two basic types, internal and external. Internal hard drives are used inside computers and laptops to run the operating systems. External hard drives are used outside computer systems to store data. External drives connect to computers via a USB cable. External hard drives have type sub types, desktop and portable drives. Desktop drives are regular drives while portable drives are 2.5 inch hard drives made for portability. Hard drives use different parts like PCB, heads, platters and spindle motor for operations. These drives have a long history of failure especially when dropped. Although any kind of hard drives can fail but these traditional drives have very fragile heads and that is why if they are operating, a little movement can cause serious damage. As a whole these drives have long life cycle.
In internal drives there is a new family of drives called SSD (solid state drives). SSD drives use memory chip for data storage just like USB flash drives. These drives are considered faster and more reliable but in fact these may be fast but not as reliable as other drives at least at the current stage of the technology. These drives can fail electronically or logically. The life cycle is also short because of the memory chip usage. These SSD comes in different capacities. Because SSD drives are at their initial stage, these are very expensive at the moment. The technology needs a lot of improvement. SSD drive memory can disappear as time passes. Data Recovery from these drives is very expensive. These drives are used in both PCs and Macintosh computers.
The next type is Raid technology. It’s not really a type of the hard drive but a combination of hard drives for better performance and storage. Raid is a combination of more than one drives in order to increase processing speed and to minimize data loss risks. The other form is network drives. These are also called NAS (network access storage). NAS drives are used over network in order to store data. Both NAS and Raid use windows and Linux operating systems. Data Recovery process involve repair drives by changing parts in case of physical damage. The process is usually expensive.
The next type of data storage is called SD cards. An SD card is a small flash chip that store data in portable devices like phones, camcorders, digital cameras. These cards also use flash memory for data storage. Data recovery process involves both logical and physical recoveries. They come in 4, 8, 16, 32 and 64GB sizes.
In this article I have explained about data storage devices like hard drives, USB drives and SSD media.
Startup Password
Sometimes computer are hacked and are locked with windows startup password. This password is not the windows password. It is encrypted windows password and is not easy to remove. The pop up windows shows " This computer is configured to require a password in order to startup. Please enter the startup password below". This password is also called as Syskey password. Computer and laptop repair Mississauga can help remove this kind of password.
Solid State Hard DrivesIn this article, I will talk about solid state hard drives. I will also explain some other facts related to SSD hard disks.
Solid State, also known as SSD are the latest media that is being used for storage. These drives do not used traditional parts like heads, platters or motor spindles. These hard disks consist of memory chips, a controller and a system board. The read and write operation in these drives, is fast compare to regular media devices. Data is stored in multiples chips installed on an electronic board. Data in memory chips is controlled by another chip called controller.
Many companies make SSD drives but the actual chips are manufactured by just a few companies. A flash drive and an SD card is a type of SSD family. A USB flash drive works the same way as an SSD drive. There are mainly two differences between an SSD and flash drive. The first one is the connection interface which is a USB (slower) compare to a sata connection (faster) on solid state media. The second one is the memory capacity. SSD can save larger amounts of data while a flash drive has limited storage. There is one more minor difference between the two and that is, a flash drive or SD card have limited number of (one to two) memory chips while solid state has more (four to sixteen).
Solid State drives are expensive. This is due to two reasons. First, it is a new technology and second, it is more attractive to users because of its speed which means there is more demand for them. If a computer’s operating system is installed on an SSD, it will load fast. It’s also stronger against unexpected moment. Unlike other traditional hard disks, these drives have no moving heads and motor which makes them reliable in the sense that in the event of accidental physical moment, heads will not crash on platter (making them unrecoverable when it comes to data recovery). Solid State media is being used in Apple’s Mac computers like iMac, MacBook Pro, Mac mini etc. Flash media is also being used in iPhone and iPads in addition to Microsoft PC desktops computer and laptops.
There are several drawbacks of these drives. Operational reliability is the number one bad aspect. We think that these drives are safe and nothing will happen to them. It’s not right. These hard disks work the same way the traditional hard drives work. These have power and electronic boards. These use indexes and table the same way like others. The data can go corrupt as a result of controller malfunction or any other reason. The tables can be damaged. The controller can be bad as a result of power surge. The data in the memory chip can vanish because of electromagnetic forces. The board can go bad as a result of design flaw or power problems. These drives are usually hard to repair. There is no guarantee of data retrieval after a long period of time because the data may disappear automatically. Data recovery from these SSD drives can be very expensive because of readability problem of multiple chips and other drawbacks. And yes, this media is expensive at the moment. There are so many other problems with this technology because it is not mature yet.
In this article I have described what SSD drives are, how these operate in addition to their benefits and drawbacks.
Cryptolocker, a Dangerous Computer Virus
In this article, I will discuss a very dangerous Malware or virus that is different from other viruses.
As the name indicates, this virus will kind of lock users out. It’s a kind of malware that first infect the system and send information to the creator or author about a particular computer. Then author server than assign a specific id to the machine and generate a pair of public and private key. The virus first look for all kinds of file extensions (like word, excel, PDF and photos). It looks for data files on the infected computer, USB flash drives connected to it and any network storage. Once it determines what files to target, it then encrypts them with a public key and displays a popup on the main screen. The files can still be seen with original names and file size but when the user clicks to open them, it would display a message that “the file is damaged or is not the right file format”. The popup says something like this “your files have been encrypted. If you want to decrypt them, you need to pay $300”. It then starts a clock that goes backward from 72 hours and as soon as the 72 hours time is passed, the private key, they say will be destroyed and files will never be decrypt able.
The way hackers ask for money is the same as another type of virus these days, where the malware fills the whole computer screen with a window with a very legitimate looking notice from the government saying something like “you have been involved in illegal activities and pay $100 via ucash at certain gas stations”. The hackers ask users to pay the money using two methods. One is a virtual voucher and the other one is prepaid card kind of thing. These two methods are time consuming and it is believed that, the time not enough to complete the process. This caused a delay and the hackers changed their strategy. They started online customer service offering the user to pay more money ($2300). So far there have been no reports if someone has actually paid and decrypted their files.
Who are and what kind of computers, are the target? Research shows that businesses are mostly affected. The virus is sent via email attachment. The virus runs its processes in the background without the user knowledge. So far all PC computers, laptops and servers are being affected. There have been no reports of attacks on Apple Mac computers and MacBooks. Mostly those computer are infected which are not protected with a good antivirus and firewall. When a computer or laptop is infected with a virus, it’s not easy for the user to get rid of it but computer experts can remove it without any problem. A computer technician usually uses different tools and antivirus programs to clean an infection. In the worse case, a computer can be backed up and then wiped out to remove malware and viruses but Cryptolocker’s damaged cannot be undone. It’s the most serious data destroyer.
What is the line of defense against Cryptolocker? What we need to do to avoid this kind of irreversible damage? Data recovery is not possible after its infection because the private key is stored on hacker’s servers. In regards to protection, first of all every windows computer must be protected with a good antivirus like Norton etc. Second, email and email attachments should not be opened. Hackers are using so advanced methods to trick people that, a lot of time, computer users are trapped resulting in a serious infection. Every user should backup their data to an external hard drive and disconnect it from the computer because if this virus exists, every backup attempt will update the old backup with the infected one. Online backup is not recommended. Online backup is updated regularly which overwrites data with the infection one. USB flash drives should not be connected to the computer all the time. If you got this virus, please contact us as soon as possible.
How a computer gets a virus infection
In this article I will explain how a user’s computer or laptop catches a virus. I will also talk about virus prevention and precautions.
The use of computer is expanding day by day. There are so many types of computers like desktop computer, laptop, iPad, tablet, Apple computer system, cell phones and others. Most of these computer machines can get virus infections in one way or the other. More than 80% of the world market uses Microsoft Windows computers. There are thousands and thousands of viruses, malware, adware and scripts that have so far infected millions of computers and notebooks.
How a virus attacks a computer? The way the virus transfer into a computer system is very annoying for a normal user. The attack is mysterious and destructive. As we know a virus is a computer program that can do anything the author wants it to do. Computer program has two aspects. It can run visually so that user can see it on the screen and it can also execute in the background which is the dangerous part of programming because a user cannot see it. A computer virus can execute the same way as installing a normal program on a computer. The difference is, a normal installation can be seen in the form of install wizard while the hidden execution cannot be noticed. So the virus can install itself automatically. This means, the virus copies all its files on the user’s computer without visually displaying the install wizard. Once the virus is installed, it can be run in a variety of ways like executing itself when the windows system starts. As mentioned above, the Microsoft Windows contributes to 80% to the world market that is why there are so many windows threats on the internet. The new type of computer that is safer against viruses is the Apple’s Mac computer, MacBook and MacBook Pro. I have seen attacks on these computers too but overall the number of infections is almost zero.
Let me explain some popular ways how a virus can execute without users permission. As explained above one way is, it can start when the computer system is started. A lot of times, user downloads free programs from the Internet. According to a research more than 10 percent of total websites are infected with some kind of code that can infect a system accessing that site. These websites change their malicious code regularly so that the antivirus programs cannot detect it. So when user downloads a program from the internet, it is usually in the form of a package and can contain anything including adware or agent programs used to communicate with virus developers. The virus can also attack a computer when a user opens an attachment. The email looks legitimate but in fact the attachment contains dangerous virus. There are different kinds of viruses starting from basic to the most destructive ones.
How to clean and protect against viruses? Once a machine is infected with a worm, most of the time it can be cleaned. Many antivirus companies offer all kinds of tool to combat certain types of threats like stinger by Mcafee, tdskiller by kesperasky, power erase by Norton, Software Malicious Removal Tool by Microsoft. All these tools only work against some known infections. These companies also offer full versions of antivirus software. Which one is better? Nobody knows. The best defense is precaution. I will talk about precaution in the next paragraph. It’s very important to show your computer to a computer repair professional once it gets a virus instead of trying different things. This may avoid further complication.
So what are the important steps to avoid viruses and malware? First of all, the windows must be up to date i.e. windows updates should be installed all the time. Second a good antivirus with a firewall must be installed and up to date all the time. The next step is to avoid opening emails and attachments from unknown people or unknown email addresses. The most important one is this one. Let’s imagine, a user visits an infected website whose integrity was not known before and he or she opened it, the machine may get some popup window or the system might suddenly slow down. The best defense will be to press ctrl+alt+delete and force end all the running programs and avoid visiting that site. Some antivirus programs have the ability to feel this kind of infection and that way the user can close the website immediately.
In this article I tried to educate users on how a computer gets infections and what to do to avoid them. I also described about different types of virus attacks.
For virus removal please call us.
Virus / Ransomware Alert:
Be aware of what I call it, the most dangerous virus in the world. I have never seen such a virus in my 24 years experience. This virus is in the market for a while now but more computers are being infected these days. What happens is, these hackers download a program into the target computer, which then encrypt all the data including pictures, documents and videos. After encryption, the decryption key is sent back to the attacker. After this nothing open properly. There is absolutely no solution for this problem unless someone get that key which is only possible when the attacker is paid a huge amount of money. They leave a file on the desktop which shows procedure how to send money. These days, they are sending emails to trap people. The email seem interesting or full of surprise. As soon as the user opens the attachment, the computer get the virus. The best way to protect a computer is to have a firewall and up to date windows and antivirus programs. Do not open links, attachments, emails from unknown sources.
What is the best way to backup a computer?
In this article, I will talk about some of the best ways to do data backup. I will also explain the importance of data backup.
Data backup is compulsory for all computer users. When I say data, it could be anything from writing some notes to a high level corporate records and databases. It is important for every computer user. Every single computer, tablet including iPads, iPhones etc. deal with different kinds of inputs like pictures, documents, music etc. Data for a writer means, hours of writings, and data for a household is all important photos or pictures and videos. A small business maintains its financial info including customers' database, employees’ records, inventory and any other office documents. Medium and large corporations have huge amount of crucial financial and company information. Whether it's small business, a household or a large company, nobody can afford to lose their important inputs.
How data is usually kept? There are two tradition ways people keep the information. One is a hard copy and the other one is a soft copy. A hard copy can last up to a certain time. A soft copy can stay for a long time depending on method of storage. In old times soft data or electronic data was kept in the form of punched cards, while the modern methods include data storage on magnetic media using CDs, hard drives or USB media.
CDs storage is not long lasting usually after 8 to 10 years, information starts to disappear. Traditional hard drives can keep data for a long time. USB and SSD drives keep data in nand memory chips. It’s also not a very attractive way to store data online but the attraction is unfortunately not that good. The reason is it costs money to store documents, pictures and photos using online services. This means if a user pays $10 a month for online data storage, it will be $120 a year and if he or she keeps the data for 5 years, its $600. I am not talking about 10 to 15 years which will be $1200 to $1800. Here is a another bad thing about online backup and that is, the user agreement say it clearly that in case of accident, the storage service will not be responsible for data loss. One more problem is, if the Internet is not available, there is no way to access data for emergency purpose. Another important aspect is to keep private and confidential data on someone else computer online is definitely not a smart move. What if a service stops its operation all of a sudden due to any reason? Yes the user will lose his or her data because there will be no chance of Data Recovery.
So what is safe and better way to store information? Definitely, the best strategy will be storing data on an external hard drive or USB in addition to one copy on a computer, laptop, iPad or phone. This means every user whether he or she uses a computer (Microsoft windows or Apple), tablet, laptop or any other device, must have an external hard drive. It's cheaper, reliable and more convenient way. How it is convenient? All Apple computers and Microsoft Windows computers have built-in data backup utility. A user can easily run the wizard to setup an external hard drive to backup the computer whether it's a Mac computer or PC laptop. The first time it takes a few hours to backup the entire data. Next time only updated files are backed up and user cannot even feel it. This way all the documents, photos and music is saved to an external hard disk without user intervention. This is no doubt a best way of computer backup.
In this article, I have explained different ways of backup. I have also discussed the most recommended method to backup a computer.
Cannot install hp all in one photosmart printer due to the following error
"The installer cannot access this registry key. Please ensure the installer has access to the registry and click Retry to continue installation. Registry Key: HKEY_LOCAL_MACHINE\SYSTEM Manufacturer: Microsoft. "
This solution is about hp printer installation on Windows 7. It's a very easy fix. There are alot of solutions discussed on the Internet. Here is the simple solution. Right click on the hp printer software setup file and click properties. Clisk on compatibility tab and then choose Windows Vista SP2 from the drop down menu and click ok. Now go ahead and install the printer with "run as administrator" option. That's it. Hope it helps.
Apple data storage and recovery
Apple computers and tablets include iMac, MacBook, Mac mini, iPhone, iPad and other popular products. In this article I will talk about data recovery from all these products when they fail.
Apple computers and tablets are getting popular now. According to my personal opinion, more than 20 percent of the market now consists of Apple desktop computers called Mac, MacBooks, iPhones and iPads. These machines use traditional and new types of hard drive storages including internal and external. In internal they use traditional hard drives (drives with moving parts inside) and flash media. Data storage is one of the most important factors in personal and business use. In fact Mac computers are being used equally in business and for personal use. Businesses use them as servers and stand alone work stations in addition to vast use of Apple tablets by business executives. Talking of personal use, there is a huge end user market for Apple products (the most popular are MacBooks, iPhones, iPads etc.).
Apple computers and laptops uses two kinds of storage media, a regular SATA or IDE drive and solid state drives. This is a fact that Apple MacBooks are well built and physically strong machines. So most of the time users think that nothing will happen in case of minor physical damage (which is true for the over all body of these MacBooks) but in case if these machines have traditional hard drives that use heads and platter then chances are the drive may receive a fair amount of damage making is hard for the machine to read it. The situation gets worse and worse when the same sick drive spins with every single use. On the other hand if the iMac or MacBook has an SSD known as solid state drive then physical damage wont do anything but as SSD drives are based on the same logic as the traditional drives are built, the data corruption is always possible.
So what happens if the drive fails? The best strategy is to backup data to an external hard drive. This way, two copies of the data will be available locally. Online backup has emerged as a replacement of local backup but it has a lot of drawbacks. If the Internet drops for sometime or if the online backup is not accessible then it becomes a huge problem. Also online backup is risky in the sense that when a user signs up for online agreement, the agreement clearly says that “in case of accidental data loss the online service will not be responsible”. This makes online backup a dangerous activity. Also a majority of computer users do not want to share their private data with online world. So what happens if there was no backup and the data was crucial? Data recovery becomes the next option. Apple computers are very good and reliable products but hard drives are from third parties which can fails anyways. In case of data loss, data recovery can be performed. There are two ways to do it. One is a logical data recovery that is done when a media is damaged as a result of file corruption. It is advised to use the software recovery very carefully as some software write to the media which will make the recovery impossible. The next stage is the hardware recovery which can be performed in clean rooms by professionals. In hardware recoveries, two techniques are used, by repairing drives using working parts and by using professional data recovery tools or machines.
In this article, I discussed about storage media used in Apple computers, Laptops and tablets and different ways of dealing with the data if it is lost.
Mac hard drive repair
Mac Computers and MacBooks are made by a California company called Apple. These include MacBook Pro, Desktop and tablets like iPhone, iPod and iPad. I will talk about repairing hard drives used in these machines.
MacBooks and Mac desktops including iPads and iPhones are very popular products these days. The number of market share is growing. More and more users are getting attracted towards Apple machines. These machines includes a variety of apple products like iMac, MacBook, Mac Pro, Mac mini, iPhone, iPad and iPod are a few to name. Apple uses both kinds of hard drives in these computers i.e. normal drives with moving parts and modern hard drives. When it comes to internal drives, they use SSD and regular hard drives like SATA or IDE. In external they make Time Capsules in which they use SATA drives. As we all know people store data on computers for all kind of purposes like personal and trade purposes. The usage of Apple machine is very common whether it is personal or business. There are multiple uses of a Mac computer in business environment. Data is stored on enterprise server machines in multi user environment. Company employees use all kinds of tablet machines like iPads and iPhones. The number of residential users is growing fast. Mostly users love Macbook Pro, iPad and iPhone. A large number kids use iPods and iPads. Schools, Colleges, private and semi private organizations, restaurants and Industrial sector all use these Apple products.
There are mainly two types of hard drives used in Apple computer. One is called SATA and the other one is IDE. They also use SATA types in SSD drives. SSD drive is a new type of storage media that is fast. Apple computers are considered strong to sustain damage. That is one of the reasons why the cost is more as they use better components in these machines. When it comes to hard drive storage anything can happen whether it is Apple computer or Microsoft base PC desktop or laptop. The danger is more when regular drives with internally moving parts, are used in Mac computers which is mostly the case in most of Apple computers although they are moving fast toward SSD technology. In any case, the drive can always fail as a result of physical damage or any other electronic damage. Liquid damage or manufacture defects are other two reasons for drive failure. Let us assume that a Mac computer has an SSD drive in it, can it fail? Yes, the drive failure is still possible because SSD drives use the same logic as other traditional drives use except platters and heads. New Mac computers like iMac, MacBook Pro use SSD drives for data storage. Data corruption is possible because of a power surge. There are other reasons which trigger the need for data recovery like formatting the drive by mistake or any other corruption of files system.
So the interesting question comes up next and that is what if the storage media stop working or there is a need for hard drive repair? What need to be done to avoid it? Well backing up the computer to an external hard drive is the most popular and safe technique. Why it is the best technique? Because this way data is available locally and without compromising it’s security. Best off all if the computer fails, a copy will be available on external drive. There is this online backup trend emerging. I was told by one of my client that his data disappeared all of the sudden from an online service called Drop Box. Online backup is not a very attractive way of saving data. You have to have Internet up and running one hundred percent of the time to upload data. Even after the data is backed up and if the Internet connection goes down and there is a need for data, nothing can be done. There is another problem with online backup. Users are asked to sign or accept an agreement (which normally users do not read as nobody has time these days) but the interesting fact is, the agreement clearly says that the online service will not be responsible for any data loss in case of an accident. This is the most dangerous aspect of online backup. Another reason of online backup failure is, most people do not trust to store their private and confidential information or photos on someone else computer or online server. In case there a hard drive dies and there is no local backup, what is going to happen? Data recovery is performed on failed hard disks. There is no doubt that Mac machines are strong and durable but drives can fail any time which can be repaired or recovered properly. There are different kinds of data recovery processes. One is called a software recovery and the other one is hardware repair which is usually caused when there is a physical damage on a hard drive. Software recovery can be very attractive option for beginners but some times it can further destroy the data. Therefore it is always advisable to let data recovery professionals perform the data recovery service. The hardware recovery is the process of repairing hard drive in clean room environments. Hardware recoveries are well performed by professionals who either recover drives using data recovery machines or by replacing parts.
In this article, I threw light on data storage devices that are commonly used in Mac computers and discussed different methods to backup data and how to repair hard drives.
Computer Spyware infection and repair
In this article I will talk about computer spyware and malware and how computers are attacked by these malicious threats.
Computer virus is software or a program that can do anything as planned by the creator. All computers in the world follow simple instructions that are developed in computer language. A PC computer runs on a windows program. A Microsoft word is a program that helps create word documents or excel documents can be created by the help of a Microsoft program called Excel. A virus, Malware and Spyware or adware are programs that are developed for specific purposes. Viruses are mainly made to attack Microsoft based PCs and laptops as they are being used at large scale in the world roughly around 70% percent of all computer market. In the next paragraph, I will explain why people make viruses and how they mange to spread these programs.
Computer users ask me all that time “why people make viruses?” I will share the answer with the online world in this article. There are multiple purposes of viruses and spyware. The number one reason is to steal important information from others computers without user’s consent. This information includes but not limited to identities, photos, documents like passwords, email addresses, banking information and more. There are a lot of programs on the Internet that look for music and movies online. I heard a story about a virus where a guy made a virus to help her mother’s computer repair business. He made this virus and shared it online and it spread on the entire Internet. There are some destructive programs that are in the news these days. The most destructive one is the crypto locker. The creator made a program that mainly attack business computers and encrypt anything that it finds on business desktop computers and laptops. After encrypting the data, it then sends the master key to the creator who then sends a notice to the user saying that “in order to decrypt the data, the user has to pay certain amount ($500-$2400)”. A data recovery in this kind of attack is almost impossible. We get cases like this most often. Another type of virus or spyware program includes software developed for stealing address books. Users are usually deceived by telling them to click on some important links in emails or face book and then malware is installed without user’s notice. Some people make viruses for fun. They think bothering others is a fun unfortunately.
The question is “how the virus can be installed on a computer?”. User always think their computer has no infection because they have security software (antivirus) installed. Well let’s talk about how the virus gets into the computer. As explained above, a virus is a simple program that can be installed on a computer in two ways. One is the visible installation that is the user can see the installation progress. The other way is to install the program in the background. How is this done? Well program installation is the process of copying files on the computer and this can be done easily in invisible mode. This is true for every operating system whether it is a Microsoft PC, laptop, Mac or MacBook Pro. It is true that Mac computers have less or almost no viruses but more and more programs are being developed for destructive purposes these days. The reason why Mac computers have fewer viruses is their market share and the operating system architecture. In the future when there will be more and more Mac desktops and Mac laptops, there might be more people to attack them but it is not the case right now.
So people ask the question “why their computer got a virus or malware when they have an antivirus?”. My answer is, everyday thousands of virus programs are written and it is not possible to update antivirus database to protect against these viruses which makes the detection process impossible. So what is the best way to protect against these threats? Well it is very important to have the latest operating system with latest updates. A good antivirus with firewall is a must. The antivirus must be up to date all the times. The browser must be up to date. Those users who have Windows XP computers must update to the newer version of windows and let say they cannot update windows, they should be using an up to date browsers like Firefox or Google Chrome (the reason for that is, they cannot update their browsers after certain version). This is extremely important.
Let’s talk about the nature of attacks and symptoms. After a computer gets an infection, user usually see lots of popups. The computer would freeze. Sometimes the computer would show very strange symptoms like restarting, blue screen, black screen. Some viruses and malware would cause opening the browser automatically. A virus can damage files or operating system in different ways. If it damages the file system, the user’s data may not be accessible. Some malware or viruses can damage a computer hard drive and data recovery might be needed if this happens. Sometime a virus can do strange things like display everything upside down. It can also damage device drivers like mouse driver, keyboard, video and sound or network drivers. In such cases these drivers are reinstalled but mostly the damage is so severe that everything has to be reinstalled including operating system and all applications.
In this article I talked about viruses, malware, spyware and how they attack computers and how to repair computers infected by these threats.
How to setup automatic backup in Windows
First of all connect your external hard drive to your computer.
Click on start menu and click on “control panel”. In control panel double click on “backup and restore” icon. This will open a new wizard as shown in the picture below
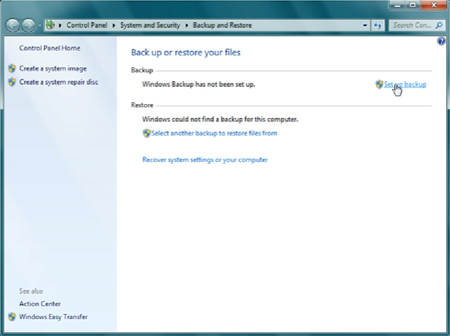
Now click on “Setup Backup” located in the right upper corner of the wizard. This will open a new window titled “Select where you want to save your backup”. In the list as shown below, you will see your external hard drive
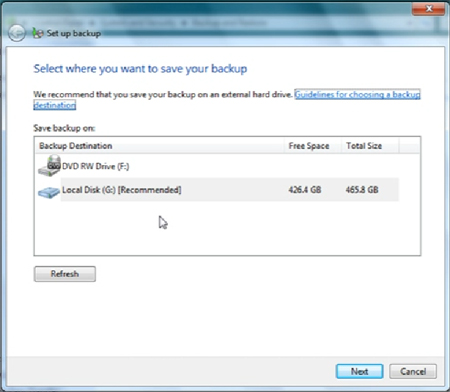
Select your external hard drive and click next. You will then see the next window as shown below.
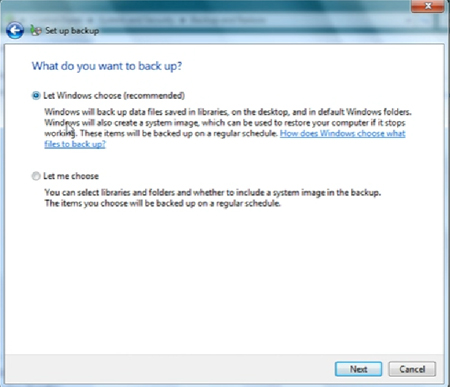
In the above window, you can see the question “What do you want to backup?” If you have problem what to do, just select the first option and click next. This will backup all important folders on your computer and it will also clone the whole drive into one file called image. It’ kind of two types of backups in one shot.
If you want to keep the backup size small and help computer to do it quickly instead of copying some unnecessary data, you can select the second option (“let me choose”). When you click next it will give you a screen where you can uncheck unnecessary items and choose your required folders to be backed up as shown below.
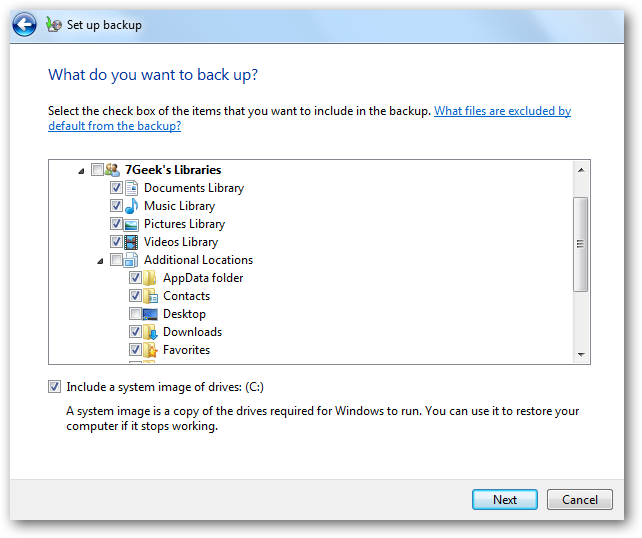
Now review your setup as you can see in the below window. Whatever option you select click next.
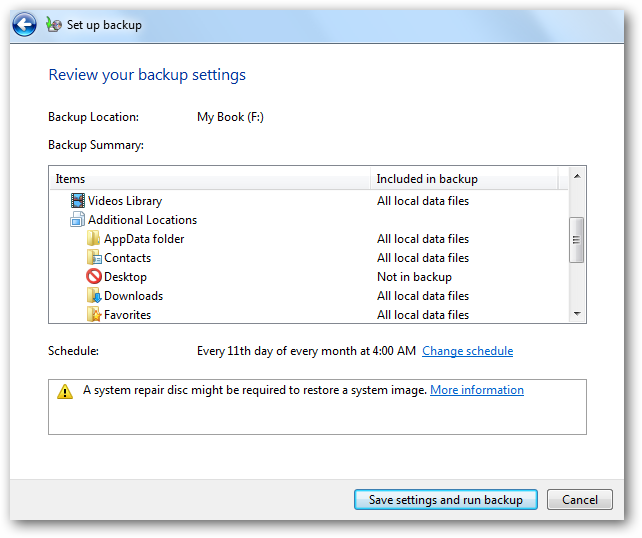
As you can see above, click on “change schedule”. This will open the below window. You will see the last question “How often do you want to back up?” This is the schedule. Here you can define what day and time (see the below window) the computer will perform a backup. You can choose run daily, weekly or monthly at any specific time. You can choose any time round the clock.
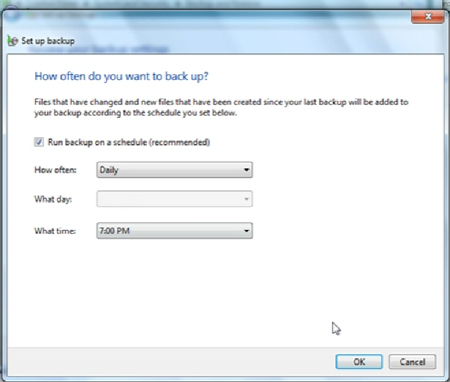
Click “OK” and this will take you back to the previous window where you click on “save settings and run backup”. It will take some time depending on the size of the backup and next time, it will only backup when contents are updated. You won’t notice the backup process and you won’t have to worry what to copy and what not. This is an amazing way of securing your crucial data.
Source: http://www.computerstar.ca/computer-mac-laptop-datarecovery-help.html
If you need any kind of computer repair help, please visit our computer repair store in Mississauga, Ontario
Benefits of automatic backup:
- It is automatic so when you update your files, they will be automatically backed up i.e. only updated content will be added to the backup.
- You will have one copy of your data on your computer and other on the external hard drive
- Your backup will be available to you even if the Internet is not available
- Your confidential files will be stored on your own device instead of someone else computer online
- This local backup wont cost you anything except the one time cost of your hard drive which means you don’t have to pay for online backup service every month
- You have the most secure setup now because if one device (your computer or laptop) has problem, you will have second copy on your other device (external hard drive). Cloud / online backup agreements clearly state that, they will not be responsible for any accidental loss of data.
- Data transfer rate is fast even if your Internet is slow as it has nothing to do with Internet
- You can move with your data on the external hard drive if you want. You don’t have to look for Internet access while you are traveling.
- If your computer crashes or if you have to reformat your computer, you can easily transfer your data back to your computer without Internet access.
- You can schedule your backup i.e. you can tell the computer when and what to backup automatically
- With automatic local backup your data is not at risk
- You probably won’t need a data recovery service as you would have two copies of your data
What you need in order to setup automatic backup?
1. One external hard drive (500GB, 1000GB or above as per your requirement). The rule of thumb is, let say your computer has a 500 GB hard drive then a 500 GB external is more than enough. For a 1TB computer hard drive, you may choose a 1TB (1000GB) external hard drive.
2. A computer or a laptop
Free Great computer tools
In this article, I will try to share my experience about free computer and software tools available on the Internet.
Microsoft office suite includes ms word, excel and power point. New computers usually come with trial version of Microsoft Office. Buyers had chance to buy office after trial would expire and if not then they would have nothing to edit or make new documents. Now there is a great free alternative of word, excel and power point. It’s called Open Office. It can be used to make new documents and can also open documents made in ms word, excel and power point. Open office works for both windows and Mac. It can be downloaded for free from openoffice.org.
The next free and great tool to use is Picasa. It’s a free photo editing tool. That’s existing photos can be changed and saved. It can also be used for organizing photos in the form of albums. This tool is being offered by Google. It can be downloaded from Google website. Another alternative for photo editing is Adobe Photoshop but it is not free. A trial version can be downloaded for testing. It’s usually not cost effective for personal use because it is normally used in professional work.
Audacity is the next tool that is very nice and on top of that it is free. This tool can be used to convert audio into a computer file. The user needs a mic and a computer and any sound can be converted into a file. In other words, this tool can be used to store data on computer. The tool has a lot of control to balance the audio. This is a great tool to transfer audio memories to CD, USB, laptop and desktop.
The next top free tool is Panda Antivirus. I have personally tested it and is great against malicious websites. A lot of spyware and viruses come from websites when users visit them. This antivirus has passed all its tests compare to other free and famous antivirus programs. It can be downloaded from cnet.com or by searching for free panda antivirus in Google. There is no need to buy the paid version as this free version is excellent. This antivirus has all features like schedule scanning, real time detection and works great against infected websites.
Now I will talk about data recovery tools. There are many data recovery tools available on Internet but unfortunately there is nothing easily available that is capable of recovering data in an acceptable way. There are so many sites that sell phone recovery and hard drive recovery programs but most of these programs actually don’t even work or recover data. They usually offer a trail but there are problems with trail versions. They show files after scanning but that is not sufficient because recovering file names does not mean the files will be good and in order to see whether the files are good or not, these files must be opened which can only be done when the program is bought. It is my personal experience that these websites actually lie about their products and a lot of them have copied other fake product and change names but in reality they don't recover useful data. This is a big problem on the Iinternet as innocent people don’t know the real story and they end up losing money. So my advice is unless a data recovery tool can actually recover a few files and they are good, they should not be trusted. It’s always better to seek help from a professional data recovery company. Normally the job that these free or trial versions can't do, can be economically done by data recovery people.
In this article, I tried to discuss about some great free tools and their usage. I also talked about some useless data recovery programs being offered on the World Wide Web.
Data backup
In this article, I will explain what backup method is the best and why online backup should be avoided.
Losing data means losing time. Personal data is even more important which includes pictures, videos and documents. In any case data backup is needed for all kind of data. So what method may be used, online or offline? Let me explain offline method. In this method data is copied or backed up to an external hard drive, USB flash drive, CD or network shared drive. There are many online companies that office online backup. Lets talk about some of them. They charge a fair amount to offer backup services. Here are the prices per year. Carbonite $59, Acronis $199, Norton $49.99, Dropbox $99, iCloud $19.99 (1tb), one drive $48 and so on. These prices have a limit of storage. This means if customers needs more space then they have to pay even more. In the rest of the article, I will talk about these online backups in detail.
Before I get into online backup details, lets talk about what define backup. Consumers today use a variety of devices to store information. These includes PCs, laptops, servers, smart phones, tablets like iPads and other computers. All the information on these devices are usually important. People use online and off-line methods for storage. There is a lot of talk about online backup these days. It is very important to spread light on all aspects of online backup. Online backups have a lot of drawbacks. First of all it cost a good amount of money. As mentioned above, the cheapest service on average may cost $100 for every five years. An external hard drive may cost around $60 and can be used for unlimited time. Online backup works when there is steady Internet service available. What if Internet connection drops during a file copy process? Surely, it might end up saving incomplete file and thus may make it unreadable. Another concern is if something happens like accidental loss or if the company close down then all the data will be gone.
Off-line backup seems to be the best policy. It includes backing up data to an external hard drive, USB drive or shared network drive. It is cost effective, convenient and confidential way of storing information. There are two types of OS platforms, Apple and Microsoft. Microsoft products come with windows operating system on laptops, desktop computers and server. Apple product like mac, macbook pro, iPad, iPhone use OSX for operation. Both plate forms have very user friendly automatic backup utilities. In case of media failure, data recovery is possible. Most people think that off-line backup is hard to do. They think that copying data all the time is not convenient but in fact it is not the case. Setting up automatic backup both in Apple and Microsoft products is possible and it can be scheduled properly. The computers and devices will backup all the important data silently and without any disturbance. The utility takes sometime at the time of first backup and later one only newly added contents or files are saved. This way the daily backup does not put load on the computer system and thus it does not slow it down.
In this article I talked about the importance of off-line backup method. I also explained about drawbacks of online backup.
Data Loss Stages
In this article, I will explain how data loss occurs. I will also talk about different stages of data damage by human mistakes and natural disasters.
Data loss will happen one or two times in life. There are different ways data loss can happen depending on the kind of storage device. A USB device will be the cause when the USB port breaks. An SD card will get corrupt or get formatted. A CD or DVD will get scratches and won’t read anymore. A hard drive will have variety of problems which I will explain in more detail in the following paragraphs. A phone or iPhone will make us suffer when a software update will ruin everything. Sometimes we accidently format or delete important data. A child will destroy all the data by pressing a wrong key. Some times a hard drive will physically fail and will make things terrible.
Now I will talk about something every important. A hard drive can physically fail. When I say hard drive that means I am talking about a hard drive from Apple computer, drive from a Windows laptop, hard disk from a personal or business server, an SSD drive from any desktop or laptop computer. When a hard drive fails, it could be one of the few problems. It could be a bad electronics board which is called PCB. The drive can have a failed motor, firmware corruption or read / write head failure. Traditional hard drives have moving parts like platters and heads. Old hard drives have one head and one platter. As the technology grew, the number of platters and heads increased. Now drives come with 4 platters and 6 to 8 heads. So as the number of moving parts increased, the risk of failure also went up. Imagine if there was one head and one platter at one point and now there are multiple parts inside the drive, the risk of failure went up several times.
When this happens, it is very important to understand one thing and that is, take the hard drive to a data recovery lab where the data can be rescued for a much lower price and the risk of losing data permanently may be tremendously reduced. This is a fact that many end user don not understand. They try different things and this make the situation worse, even keeping the drive for a long time make it worse too. I have seen many cases where different computer repair people tried to recover data without using proper tools and made the recovery impossible. So my advice in this case is, when a hard drive gives problems and the data is important, it must be taken to a hard drive recovery professional place to save big time trouble and cost.
There are some other important precautions that must be exercised before it’s too late. For example many people update there iPhones and iPads when they see an update alert. They don’t know the consequences if the update process fails which unfortunately happen most of the time. Therefore it is important to first backup all the data and then run update because in case of software corruption the only way to bring the phone back to life is to restore it to factory settings and there is no way to recover such a phone that has been reset to default. One can imagine how dangerous it is to update a phone without having it backed up. A lot of people think that when data is deleted or the device is formatted, it cannot be recovered, this is not true of course it is sometimes possible in case of modern drives where the device has some feature that allow no recovery. One more area that can save the data is, when data is deleted for any reason, it is very crucial not to use the device because using it will write data to the storage device which might overwrite the old data and this it is destroyed permanently.
Parts inside a Personal Computer
In this article, I explained about some the most important factors that can avoid losing data permanently.
A PC consists of many parts that can be repaired or replaced. This includes a casing that is the outside of the PC. A PC usually has three essential cables which include a power cable, a keyboard cable and finally a mouse cord. If we look inside the PC we see many parts. The first one is called power supply where we connect the power cord. This unit power distribution function inside a computer system. The power supply connects to a blue or green color board normally known as motherboard which is also called as logicboard, a term introduced by Apple in their Mac desktops and MacBooks. As the name suggest, this board works like a mother that help connect all PC parts together. The next part inside the box is the RAM (Random Access Memory). This part helps computer run its programs as long as the computer us turned on. The number of RAM sticks can range from 1 to 6. The next part is the CPU. The CPU normally has a fan and a heatsink (which take away heat from the CPU with the help of fan) on top of it. CPU is usually confused with the PC box or tower. CPU is the part that processes all operations for example all programming is executed inside the CPU. The next one is the graphics card. The graphics card has two types. Some PCs come with a built-in video chip (graphics adapter). This part actually displays all the programming or processing results on the computer screen. There are some extra ports in PCs that can be used to install a dedicated graphics card that does the same function like a graphics adapter i.e. displaying output on the screen (I will explain later what a monitor is).
Other parts that can be installed in these ports could be a modem, a USB splitter, a sound card (most of modern computers are coming with built-in sound card), SCSI card or a wireless PCI card (used to connect the PC to a router without wire for Internet connectivity). The other part that is most important is called a hard drive. The hard drive stores all data, programs, files like photos, documents, videos and other data. Old computers also come with a device called CD or DVD drive. This is used to copy data from and to a CD or DVD disc. This device can also be used to install programs on the computer. A Floppy diskette drive was part of very old computers. This was widely used when there was no CD or DVD drive. It is not coming with new computers anymore. There are some peripherals that are partially parts of a PC system. These include USB flash drives, Printers, Scanners and some other parts. The USB flash drives can be connected to the USB port of a PC. These flash devices are used to store data for mobility purpose. The printers are used to print, scan and send faxes. The last but not the least is the monitor that shows all the results and outputs. This device connects to the video adapter or graphics card on a computer.
Now let me talk about computer repair. A Power supply can be one of the several reasons of no power in the PC. When there is no power, the PC can be brought back to life by replacing its power supply. If a motherboard is dead, there will be no life in the system. This could be repaired or replaced. About RAM, because there are more than one RAM slots, usually one or two chips might have problem so those can be replaced or if there is a problem with the RAM slot then a quick solution would be to install bigger RAM in one of the good slots. The CPU can be replaced in most PCs. The same can be done with heatsink or fan. Hard drive can be changed or repair and fixed which can lead to data recovery. CD or DVD, Floppy drive, graphics card, or sound cards can be replaced.
In this article, I talked about all parts of a PC and a possible repair or replacement to fix a computer system.
Data Disaster
This article will provide important information about different data loss situations including actions that make the data recovery chances even worse, the different stages of data damage by human mistakes and natural disasters.
Overtime, data loss happens in one's life. Data can disappear in a variety of ways depending on the kind of storage device. Data on a USB flash drive may be lost if it is physically damaged. It can be in the form of a corrupt SD card or it may be the result of a formatted card. A CD or DVD might get scratches and won't read anymore. A hard drive may have a variety of problems (more details in the following paragraphs). A phone or an iPhone may be the cause of data loss as a result of failed software update. Sometimes one can accidentally format or delete important data and accidents by a child's mistake can destroy all the data such as pressing a wrong key. Other times, a hard drive may physically fail and will make things severe.
Regarding to dire importance, a hard drive can sometimes choose to physically fail. When saying hard drive, that means a hard drive from an Apple computer or a Windows laptop which may be a hard disk from a personal or business server and an SSD drive from any desktop or laptop computer. When a hard drive fails, it could be one of the few problems. For example, bad electronic boards (also known as PCB) or head failure. The drive can have a failed motor, firmware corruption or read head failure. Traditional hard drives consist of moving parts like platters and heads. Old hard drives used to have one head and a platter. As the technology improved, the number of platters and heads increased. Now all modern drives come with multiple platters and heads. This means more moving parts; high risk of failure and with the passage of time and moderation in hard drive manufacturing, the risk of failure goes up.
When hard drive failure happens, it is very important to analyze the situation carefully. If the data is important, it is best to take the hard drive to a data recovery lab where the data can be rescued. This decreases the cost and will increase the chances of data recovery. Due to lack of knowledge, most of the times end users fail to understand this kind of situation. They try different methods to recover data which makes the situation worse. Keeping the drive for a long period of time does not help in reducing risks. Recovery attempts without proper knowledge and experience ruin the chances of data recovery. So, general advice in these types of scenarios is when the drive gives problems and the data is important, it must be taken to a hard drive recovery to avoid cost and trouble.
There are some other important precautions that must not be forgotten before it's too late. For example many people update their iPhones and iPads devices as soon as they see an update alert. It is very crucial to first backup the data before starting the update process. They lose everything when they try to update without backup. The reason is, they aren't informed of the consequences if the update process fails. Unfortunately this failure happens most of the time and therefore it is important to first backup all the data and then run the update. This is because, in case of software corruption, the only way to bring the phone back to life is to restore it to factory settings and there is no way to recover files on a mobile device that has been reset to factory default. In simple words it is very dangerous to update a phone without having a proper backup. A lot of people think that when data is deleted or the device is formatted, it cannot be recovered. This is not true for hard drives. One most important fact is, when data is deleted or a drive has been formatted, it is very crucial not to use the device because using it will overwrite the old data which makes the data unrecoverable.
This article overall explains some of the most important factors that can avoid losing data permanently.
Hard Drive failure precautions
One of the last problems a regular computer owner wants to deal with is loosing all of their personal data. Not having the proper resources or advanced knowledge in order to solve the problem can often worsen the situation. Precautions when coming across a hard drive failure include being aware of the reason of failure, how to prevent worsening the situation and where to go to safely and efficiently to get it repaired.
The first step is to be knowledgeable about the reasons why the hard drive might have failed. This is so that; as a user, one can become more aware to the way the computer is being handled in the future to prevent the problem from reoccurring. Other than natural failure the fail can arise either physically, internally or through software. A hard drive’s physical failure can occur through wear and tearing, liquid spills, fire and mishandling. When not taken care of physically, the destruction and failure of the drive is more likely to situate and in some cases may be un-repairable. When speaking of Solid State drives, the nature of failure is different. An SSD or a USB flash drive is made entirely of electronics and can therefore fail due to a component issue on the board. Another common physical failure also happens to be the damaging of a USB flash drive. This can lead to the disconnection of the USB port. An internal failure can arise when traditional hard drives that hold motors and platters are used and ran for extensive periods of time, causing it to wear out or over work itself. Also, having a dusty environment around your device can cause the drive to ingest the dust particles and damage internal parts. The last area a drive can fail through is by its software. When corruption in the software or a power surge occurs, it can lead to further problems such as the controller going bad. Most importantly, effects that can cause all variations of trouble are viruses. A virus can go as far as to affect the drive’s inside surface. When being more aware of all these reasons to hard drive destruction, the proper precautions can be executed towards recovering your data.
The second step is to be informed of what not to do to the failed drive without professional assistance. The owner should not run third party programs, open the drive on one’s own or use multiple recovery soft wares. Running third party programs are an unreliable source to recovery and can worsen the situation whether it is from unknown hacking or viruses that can irrupt. One must also not run check disk repair, Mac disk utility or copy data especially if the drive is terribly slow. When it comes to opening the drives, if not done by a professional, it can be very hazardous and risky. This is because a drive cannot be opened without a clean surrounding environment. Some common examples of devices an owner would try to fix would be iPhones, iPads, and Solid State hard drive main boards. Doing electronic work on a printed circuit board (PCB) can cause damage to the board and will lead to further internal issues. Working on USB boards can also cause serious damage to data and chips. Lastly, trying multiple different soft wares can cause overwriting which makes data recovery impossible. In final words, its highly advised to avoid the following repair attempts, especially if the data is of grave importance.
Finally, the most important step is to take your hard drive to a trustable source for repair. By online searching, calling different sources and visiting labs, the process of repair becomes less stressful and the owner gains more secure dependability on the professional during the repair process. When conducting an online search, the best thing to do is search for data recovery in your residential area/city. After finding trustworthy resources, it is of advisory to call at least three of the different data recovery labs found. This is because a professional data recovery company has high-end tools and operators to repair properly and efficiently. The higher end the tools are, the higher chance of success in recovery. When visiting or calling different labs, doing prior research and asking questions helps to clarify and understand more of the specific issues and causes of the hard drive failure. Making knowledgeable choices and choosing dependable data recovery companies can save you money and recover all of you personal data.
In conclusion, when one’s hard drive fails; knowing the causes, preventions and proper solutions/resources can take the owner a long way and can educate them for future incidents. This in result can bring upon more awareness to safe device handling and cautious procedures when coming across hard drive destruction.
Important facts about Apple products
In this article, I will talk about some very important facts about Apple products. I will give some details about different Apple products, their features and security.
Apple computers and tablets come in different types. In desktops, iMac, Mac Pro, Mac mini, Mac servers and PowerPC G5 are among a few. Laptops include MacBook, MacBook Pro, MacBook Air and iBook. In tablets, we have iPad 1, iPad 2, iPad 3, iPad 4, iPad 5, iPad Air, iPad mini, mini2, mini3, mini4 etc. In Phones, iPhone 3g, 4, iPhone 5, iPhone 6, and 7 is on the way. Apple watch is another line of products that has recently been launched. All these Apple products are getting popular day by day. The most popular one is iPhone. iPads and MacBook Pro are also famous Apple products.
Talking of quality, it is very important to explain about software and hardware quality in Apple products. Apple computers and MacBooks use OS X. It’s the world most secure innovative program. It is so secured that it does not need an antivirus as long as the operating system is up to date. The next quality of Apple products is the hardware. The battery life is much better than any other computer in the world. The computer casing is so strong that even after big shocks, Apple MacBooks most of the time still work. MacBooks and Pro body is made of aluminum which is strong against physical damage and scratches. Logicboards used in MacBooks are of premium quality. These newer MacBooks use Apple ssd drive that is the fastest drive in the world.Most of the time, these machines can resist liquid damage. Graphics quality of screen is very good. Even a normal LCD shows the best picture which is unique about Apple computers. Retina screens are super screens in the world these days. Apple computers are getting popular due to which parts are mostly available. Also in the beginning there was software compatibility problem which is getting better and better with the passage of time.
Apple computers use secure software. The firewall is strong. Firewall can be setup to block unauthorized access. According to Apple, if the operating system is the latest and up to date, there is no need for security software. It’s true that these days, there are a lot of people trying to write viruses for computers, but it is also the fact that Apple computers are much secured than anything else. I have personally seen adwares on Mac computers but every single one of them had old operating system. There is no doubt that Apple computers, tablets and MacBooks are the most secured systems in the world. Some third party vendors have already written antivirus programs but users don’t really need them.
The prices are according to the value what users get. The overall speed of Apple computers is much better than any other computer. The boot time is fast, the shutdown time is perfect. Overall Apple computers behave like they have ssd drive installed in them. Comparing to Windows computers, Apple computer software don’t have drive issues. All the drivers are setup automatically during installation. There is no need to repair drivers because there is no question of driver corruption. Because Apple computers are powerful and graphics quality is very good, Apple computers are best for gaming.
In this article, I spread light on some facts about Apple computers, their types and features. We repair all Apple Mac and MacBook Pro families.
Intel SSD 320 Series 8mb data recovery
In this discussion I will spread light on Intel ssd 320 series failure. I will also explain how this happens and the remedy for data recovery.
After the introduction of this Intel 320 Series SSD, we came to know some drives have this 8mb bug with wrong serial number BAD_CTX. In this kind of situation, the drive cannot access data and the only solution that Intel offers is to wipe the drive but this will erase all the data. Wiping the drive is scary when there is important data stored on the media. When the drive with the above problem is connected to a normal computer, it is properly detected but it will not mount. The drive will not properly show in disk management. Drive initialization is also not possible. Updating the firmware might erase all the data so Intel help is not applicable.
If the drive has data then it is critical to first recover it. This drive has multiple nand chips that hold the data. There are some approaches to recover data from such drive. I will discuss this later in this article but the main question is, is it possible to recover this ssd? The good news is our data recovery expert has recovered this drive in the past. He did a great job by recovering everything on the drive.
This drive will show 8mb storage and the bad_ctx bug will not allow the computer to reach the nands chips. If a traditional drive has bad heads, it will either show 0mb space or 3.84 gb space. This means the head are bad. In case of ssd, it is the same situation like a bad head. In regular drive the bad heads can be replaced but if the surface is bad, then that is it but in this case our technician removed all the chips from the drive and read them one by one and successfully arranged all the nand chips to convert it into useful data. This was a very time consuming project but in the end he was able to do it.
There are three main components of an ssd drive. The main board keeps all the components and that is why it is called motherboard. The nand chips are responsible to store data in the raw format. The controller is responsible for smooth operations of the ssd. Ssd drives come in three types. One is the regular 2.5” drive. The next one is the Apple PCI ssd drive and the third one is the micro drive also known as msata drive. All these drives use the same kind of logic and when they fail same technique is used to recover them. Our technician has recovered all these three types in the past. Talking of the 8mb bug, the question is how this happens? This happens due to a sudden power loss situation. This can happen to laptops that have low battery and are not connected to a power source or laptops that have lose dc jack which can disconnect the laptop from power source all of the sudden. When the 8mb bug attack the drive, the laptop or desktop computer will give message like no boot media available and the computer will not load Windows. There are different procedures on the Internet that guide how to bring the ssd back to life but these procedures are not for those who have data on the machine. So it is very critical to take the ssd to an experienced and professional data recovery company for data recovery. If you need help with this kind of ssd failure, we can help.
In this Article I talked about Intel 320 series ssd drive 8mb bug that stops the computer from being reading data from the nand chips. I have also explained the recovery process.
Main computer keywords
This article talks about different kinds of keywords used by computer repair world. These keywords are related to different type of devices including computers and laptops.
Computer people know that there are so many computer terms used these days. Notebook service or laptop fix is one of the hot keywords. Notebooks, also known as laptops are mini computers. People, who fix computers, often use the term notebook or laptop repair, some call it notebook repair; others say laptop fix or troubleshooting. Laptops are all-in-one full fledge computers that does the same job as a desktop computer would do. Notebooks have great convenience of portability which means they can be used on the road or inside office or home.
Another famous keyword is the popular computer repair term also known as PC repair, PC services or Apple computer repair and MacBook repair. So in simple words, fixing a desktop tower or an all-in-one machine is called computer repair or PC repair. Data is what these laptops and desktop computers store on their hard drives. So if a computer breaks, chances are, the data might be damaged or destroyed. A lot of times, data can still be intact if there is a hardware problem other than hard drive failure. Hard drive is the main area where all the data is stored. If hard drive or computer fails to start, there is a risk of losing data. A famous term data recovery is used when the computer fails to start or the hard drive fails to respond. After the popularity of Apple computers, Mac repair became the most commonly used term in computer support world. As it is clear from the above statement, Mac computers are manufactured by a company called Apple. Mac computers and laptops are strong machines but in case of any problem, the word Mac repair is used.
The next component in the world of computers is the machine that gives us output on paper. It is known as Printer. Businesses use printers to print reports for day to day activities. So Printer repair is another keyword widely used by people in the computer repair industry. When a computer, laptop or a Mac hard drive fails, it creates another keyword known as hard drive repair. Every computer, laptop or Mac has a hard drive. Computer and laptops use different kinds of hard drives like SATA, IDE, SSD, Flash etc. This is the main part where everything we see on the screen is stored. Other media that store data are USB flash drives and SD cards. In old times, floppy drive, CD or DVD compact disks were used for information storage. USB flash and SD cards are faster and therefore the best invention. Floppy drives and CD drives were slow. Storage capacity was another problem with old media but the new storage devices have no such problem. USB sticks come in small dimensions but with different capacities. They are becoming small and small day by day.
Laptops and computer desktops use display or monitor to show information. The modern name of such devices, are LCD screens. Old screens were heavy and would not provide good graphics quality but new technology has better resolution and the sizes of these monitors are growing for example, Apple retina screens have the highest graphics quality in the market right now.
In the above paragraphs, I tried to throw light on different words used in computers especially when it comes to repairs. I covered old and new terms used for computers, laptops, Apple computers and MacBooks. This article was written with the intention of benefiting those who have less knowledge when it comes to computers and new technology. Most terms like laptop repair, Mac repair, PC, laptop and data recovery were covered in this article.
Computer, Mac, Laptop, Hard Drive repair questions:
Q. Reasons to have error \boot\bcd file corrupt or unreadable. This error usually shows up at computer or laptop startup. The startup screen looks like a blue screen but it is not really bsod.
A. If the boot directory or files in the boot directory is damaged, the computer will get this type of error. This directory is usually stored on a separate partition. To fix this error, the contents of this directory can be replaced with good files. This will write away fix the startup problem.
Q. Why Internet on one computer or laptop does work while there is no Internet issue on other computers.
A. This usually happens for two reasons. Wrong wifi password was entered and the wifi card is not compatible with wireless router.
Q. How much it cost to replace charging port of iPad mini
A. Change charging or lightning connector in an iPad mini is a two step process. First the digitizer is removed which in most case will crack. After that the charging port must to unsoldered and soldered which requires high soldering skills. Then a new digitizer glass is installed to complete the repair.
Q. How to know what screen is broken in an iPad with a cracked screen?
A. If the iPad is showing perfect picture and just the glass shows cracked when it’s turned on, that means the digitizer is damaged but if the picture has lines or distorted screen this would mean a bad LCD but again, if the glass has cracks then glass will also need a replacement
Q. What is the best way to backup or store data on computer?
A. The best way to deal with data is to keep two copies, one on computer and other on external hard drive. Whether it's Microsoft Windows or Apple's Mac computer, there is a built-in backup utility which can be setup or schedule to backup regularly. This process is fully automatic and it does not make the computer or MacBook slow. In Mac it only back up updated files or while in Windows, it can be setup so it only add new information to the current backup folder.
Q. What iPad mini and tab3 means?
A iPad mini is one of the first ever type of tablet that Apple invented while Tab 3 is a similar tablet made by Samsung.
Q. What tablet is most popular right now?
A. Apple's iPad is the most popular tablet on earth right now. Next is Samsung and then all others.
Q. How to resolve error message "OS X could not be installed on your computer. No packages were eligible for install"
A. This can occur if the MacBook Pro system date is wrong. To fix this, open terminal from the installer menu. Type date 0727172716 which represents July 27, 2016 at 17:27PM
Q. Websites don't open after Mac battery was changed.
A. Apple computers lose date when battery is disconnected. It's just like PC system where bios battery (5v) maintains date and other hardware configuration alive. Changing the date will fix the problem and all websites will open properly.
Q. What to do with Windows 10 upgrade?
A. Windows 10 upgrade is popping up on most computers these days. It is free till July 31, 2016. It's recommended to do this upgrade because later it will cost money to upgrade. Also regular backup of data is highly recommended. In Mac Time Machine and in Windows, Backup and restore utilities can be used to backup the system to avoid data loss.
Q. Are all Mac drives recoverable?
A. Not really. If the catalog file is damaged or corrupt, it will destroy chances of a successful data recovery. Sometimes catalog file will affect the file system resulting in damaging files and folder structure.
Q. Is it possible to recovery iPhone 6, 6s, 6 plus if they are liquid damaged?
A. Yes, we had great success with liquid damaged iPhone recovery in the past. Click here to find out more.
Q. What is the best way to protect a Windows computer from viruses?
A. Always keep the Windows up to date and install a good antivirus like Norton with firewall. This will increase blocking hacking attempts
Q. Is data recoverable if the computer is dead?
A. Yes, data is still stored on computer hard drive. Never throw your computer because data can be recovered easily.
Q. How to reinstall Windows 8 (without product key) on a computer that came with windows 8
A. Windows 8 computers and laptops store the product key in bios. Once Windows is installed, the computer automatically picks it up. The user just needs to activate it online or it will activate itself.
Q. Do we need antivirus on a Mac computer desktop or MacBook?
A. No, Apple OSX is pretty strong against threats and does not need an antivirus. Different vendors have written antivirus programs though.
Q. How to restore Windows operating system on a computer or laptop.
A. Most of the laptops and computers come with a built-in image located on D: drive which is usually hidden partition. This image can be used to restore Windows on a computer. This process will destroy existing data. So it's very important to backup all the data to avoid data loss.
A. How many types of iPad Airs are available in the market these days?
Q. As of today's date, there are two versions of iPad Air available for sale. One is iPad Air and the other one is iPad Air2. The parts for iPad Air 2 are expensive right now. For example the screen cost over $200.
Q. My computer freezes, what could be the reason?
A. A computer can freeze due to many reasons. The most common ones are, bad operating system, bad power supply, bad motherboard, bad RAM, bad battery if it is a laptop.
Q If a computer motherboard repairable?
A. Yes computer motherboard can be fixed. Different components like resisters, capacitors, transistors or other chips. These components can be replaced after proper troubleshooting.
Q. Computer repair: Trying to install windows and no luck?
A. There might be different reasons for this problem. If you are using a CD drive then there might be a problem with cd drive, the actual cd or the internal hard disk might be failing. If it is a usb, it could be the bad file system or usb itself.
Q. Plugged in, not charging
A. This message appears on laptop when ac adapter is connected to charge the battery. This could be due to several reasons. One is the actual battery, the ac charger or problem with the motherboard.
Q. Do computer LCD screens are bad for eyes?
A. All modern computer lcd displays are considered safe for eyes.
Q. What is the best way to backup an iPhone?
A. The best and the most effective strategy to backup an Apple iPhone or iPad is to connect it to a PC or Mac computer that has iTunes installed on it. It will back itself automatically.
Q. Why some keys on a laptop keyboard don't work?
A. There might be three possibilities for this problem. The keyboard might be bad, the keyboard connector may be defective or the keyboard controller might be malfunctioning. This situation mostly arises when the machine is liquid damaged.
Q. What are different ways to install Windows on a Mac laptop or desktop?
A. Microsoft Windows can be installed on a Mac computer using two approaches. One is boot camp ( a Mac OSX utility that help install windows on a Mac or MacBook) and the other one is the software environment known as virtual machine which works like a program in OSX, providing environment to run Windows.
Q. Can a screen be changed in MacBook Air?
A. There are two approaches to repair a MacBook Air screen. The first one is to change the whole assembly i.e. front and back. The second one is to change just the LCD (the front part).
Q. What is the difference between iPhone 6 and iPhone 7?
A. The main difference is much better camera in iPhone 7. About the look, iPhone 7 has two horizontal lines on the back side (one on top and one on bottom side). iPhone 7 has A10 processor which is faster than A9 processor. iPhone 7 comes in minimum of 32GB. They removed headphone jack from iPhone 7.
Q. How to reset El Capitan Password (with file vault) via terminal?
A. There is no solution for resetting Mac Password if file vault is on. In this situation, the computer does not show Macintosh HD.
Q. Can Internet Explorer be uninstalled from a Computer?
A. Internet Explorer cannot be uninstalled because it is part of Windows. Different versions can be downgraded.
Q. What is the name of Apple's latest operating system?
A. OS X Sierra version 10.12 is the latest operating system.
Q. Can Windows 8 be installed on Windows Tablet?
A. Yes, Microsoft Tablets take tablet versions of Windows 8.
Question: What Antivirus I need to protect my windows 10 laptop or PC?
Answer: According to Microsoft, Windows 10 has built-in antivirus software, so no need to install third party antivirus as long as the windows is up to date. All the updates must be installed.
Question: Can more than one OS X i.e. operating systems be installed on a Mac computer or MacBook?
Answer: Yes, not only Apple OS X but Windows operating system can be installed parallel to each others.
Question: My PC is dead, what could be the problem?
Answer: If a computer does not turn on, Make sure the power is ok. The next problem could be the power button. After that there might be a problem inside the PC. Inside, there could be a problem with power supply or motherboard
Question: Is iPad screen fixable?
Answer: Yes iPad screen can be repaired. All iPads like iPad 1, iPad 2, iPad 3, iPad 4, iPad 5, iPad mini, iPad Air, iPad Air 2, iPad mini2, iPad mini3, iPad mini 4 and iPad Pro screens are replaceable. Its usually one hour job and most of them can be repaired under $100.
Question: If a computer Windows crashes, what is lost when Windows is reinstalled?
Answer: When Windows has some kind of problem and is not fixable, a refresh is the last resort. In this case, all the data can be lost if not backed up. It is always recommended to backup all the data before erasing anything. All the programs are lost because they are part of operating system. Microsoft Office is not part of Microsoft Windows, so after formatting the computer MS Office must be reinstalled from disk. All other programs must also be reinstalled if needed.
Question: Why Windows updates take forever to install and configure?
Answer: There are mostly two reasons for sluggish Windows updates install process. One is the state of the operating system. If the Windows registry is messed up, the updates will create problems. Second, if there is a hardware problem, the updates will not run properly.
Question: A laptop is giving message "plugged in, not charging". What this could mean?
Answer: It depends from brand to brand, but mostly it's the hardware problem.
Question: Is touch screen replaceable on a laptop?
Answer: Yes, a touch screen can be replaced on any laptop. It is a bit expensive then regular screens but it is possible
Question: How to reset Android phone or Samsung Galaxy to factory settings and enter recovery mode?
Answer: Press and hold the volume up button and press the power button. Alternatively press and hold volume down button and power button to enter recovery mode.
Question: Is the new MacBook Pro battery easily replaceable?
Answer: Yes, but it needs some skill and experience to avoid damage.
Question: If a USB memory stick or SD card is broken into pieces, is it still recoverable i.e. data can still be retrieved?
Answer: Yes, if the board is cracked or broken in pieces or the everything else is broken except the memory chip known as nand chip then data can still be recovered.
Question: If a cell phone stays in deep water for many hours, is it still recoverable?
Answer: Yes if the phone was in water for a while, the data can still be recovered
Question: What is the cost of LCD replacement for a regular laptop?
Answer: The average lcd repair cost for laptops is $100-$150. This may include used or new screens
Question: How many screen sizes comes in MacBook Pro?
Answer: MacBook Pro comes in 13.3", 15" and 17"
Question: Is data recovery possible from Apple's New PCI experss SSD (solid state drive)?
Answer: Yes, it is possible. We have recovered it many times. If you need help, please visit our data recovery mississauga page
Question: What is the best laptop these days
Answer: Apple's MacBook Pro is the best laptop offered by Apple. It's good hardware, better software and battery life is excellent
Question: When was iPad invented?
Answer: iPhone was invented in 2010. It was given the name of iPad1
Question: Why aer there so many iPads?
Answer: iPads come in different screen sizes. Some of them have retina (high resolution) others have regular lcd
Question: Is iPad mini battery replaceable?
Answer: Yes, iPad mini battery can be replaced
Question: Is iPad mini dc jack repairable?
Answer: Yes, but it needs high level skill to replace the power jack in Apple's iPad mini
Question: Windows 10 black screen startup, what could be the problem?
Answer: A black screen at startup is mainly software / OS problem or video card issue
Question: How to make windows 10 log in to the desktop mode?
Answer: Go to settings, click on system, click on tablet mode, on the right window change option according to your need.
Question: Wireless connected but no Internet, what could be the problem?
Answer: There may be many reason for this problem. Some of main ones are, a software, a wifi card issue or operating system malfunction
Question: Windows 8, the windows button does not switch between tablet mode and desktop mode
Answer: Whe a Windows 8 computer is turned on, this button will not function until the user click on desktop icon to go to desktop. Once the user is in desktop mode then the Windows button can be used to switch between both modes.
Question: What Antivirus is used in Windows 8 and 10?
Answer: Windows Defender is a built-in antivirus in both windows, developed by Microsoft
Question: If a computer is dead, is the data still there?
Answer: The data always stays on the computer unless the hard drive is completely destroyed.
Question: Does solid state drive die?
Answer: Solid State Drives can die but the data recovery is always an option.
Question: What kind of technology is used in Solid State hard drives?
Answers: Solid state drive consists of nand chips, controller and a logic board. All the data is controlled by firmware which resides in controller.
Question: Why is clean room required for head transplant?
Answer: Hard drive spins at high speed and there is a small tiny layer between read/write heads and platter (platter is the surface where all data reside). If a small tiny dust goes inside the drive then it can damage the read/write head causing permanent data loss. Clean environment is always a required for head transplant.
Question: How many parts a hard drive usually consists of?
Answer: A hard drive has several parts inside and outside. The shell is the main housing, PCB is the controller board that controlls the electricity flow, motor spindle spins platters, platter store data and read/write head are the vital part of a hard drive.
Question: Does changing a PCB help recover the hard drive?
Answer: Not necessary because every PCB may have a different type/version of firmware which cannot tell the drive what to do.
Question: Computer PC is making static sound when FM radio is playing, why?
Answer: There are many causes for static sound coming from a PC. One of them is the power supply. Some power supply can make the PC to generate static sound when FM radio is playing.
Question: Why Microsoft Office disappears on a computer connected to a corporate network?
Answer: If the user takes the computer offline and connect the drive to another computer, some applications and mapped drives will disappear but as soon as the PC or laptop is joined back to the network, everything comes back to normal.
Question: Wireless sometime works and sometime does not work, why?
Answer: There are many reasons for wifi not to work. Problem with operating system, driver issue or bad wifi card
Question: What are the main features of an Apple MacBook Pro?
Answer: It is more secure against viruses, has good graphics quality, the hard drive is strong, better battery life, batter operating system.
Question: Why my Macbook cannot open websites?
Answer: Old browser is not supported by modern websites. Same is with operating system. Browser in an old operating system is always not supported because it comes built-in with the OS and it can only be upgraded by upgrading the operating system like Apple OSX.
Question: Is it advisable to use a liquid damaged laptop or desktop?
Answer: Not at all. Using a computer, laptop or MacBook Pro with liquid inside it, can cause severe damage to internal components. It is always advisable to do a proper cleanup of the liquid or dry it up if it is water.
iPhone data recovery
In this article I will talk about iPhone data recovery. I will discuss different problems causing data loss in the said device.
iPhone is the most famous device being used by millions of consumers around the world. This device is very poplar when it comes to taking photos and making videos. This device is also used for keeping notes, contacts, and calendars and for many other daily necessities. So what are those situations that can put the user of these devices in a difficult situation? There are many scenarios. Let’s discuss them one by one.
The first and the most common one is the software problem. Sure if there is nothing overwritten, the recovery process is lengthy but it is possible. Different techniques are applied to retrieve data. This process mostly involves logical solutions with one exception though. In most cases, if the phone has been reset to factory settings then it might not be recoverable but we have knowledge of some cases where data was recovered. Sometimes software corruption can cause the phone to behave strangely, a data recovery attempt is mostly successful in such a situation. This is also a kind of logical recovery. If the phone password is type incorrectly for several times, then the device will automatically go to disable state making the data inaccessible. If the password does not work this also stops user from accessing data. There are some successful data recovery procedures for this kind of problem. In some cases, the phone’s logic board heats up and this won’t let the phone to go to ready state. We have recovered a few such cases in the past.
Let’s dive into some serious hardware situations. This includes different component failure on the logic board. We all know that Apple uses high level encryption in their iPhones. This makes it even tougher to extract data directly from the nand chips. Recovery for this kind of trouble is possible. Some other problems with iPhones are touch issues. There is perfect solution for touch screen problem. Sometimes, the touch screen will work but there is will be no backlight on the phone. This is also curable. These recovery situations can be found in any iPhone model but we have recovered such situations mostly in iPhone, 6, 6s, 6 plus, iPhone 5 and 5s. Now as new model like 7, 8 and 10 are in the market, we will see more case for these models. These problems are mostly caused by natural defects or liquid damage. Liquid damage in iPhone is very common. Liquid mostly damages the logic board. I have seen many liquid damage phones and recovered most of them. This is very time consuming job and needs special tools, time and attention. The cost of iPhone recovery varies from situation to situation. It mainly depends on complexity and time spent to rescue the important data.
Sometimes lcd or touch connectors are broken or water damaged. This kind of job requires compatible parts and extensive skills and experience. A little mistake will make the data recovery impossible. It is therefore very important to avoid repairing such fragile components without enough experience and proper tools. Logic board mostly has multiple layers and damaging a single layer makes the data recovery job really hard for professionals. Many people think that once data is deleted, it can be recovered but the fact that when it is overwritten or the device has been used for a long time, the chances of data recovery go down. It is therefore advisable to shutdown the device immediately if important data has been deleted. If you are in any of the situation, please contact or visit our data recovery lab or visit our website mentioned below.
https://www.computerstar.ca/data-recovery-mississauga.html
How many kinds of hard drives are available in the market?
In this article, I will talk about some types of computer, laptop, and tablet drives that being used in these machines. These drives include old and modern drives.
There are mainly two kids of hard drives. One are traditional and the other ones are modern SSD drives. In traditional drives there are further two kinds, old IDE drives and SATA hard drives. They both have moving parts inside but have different connectors for data processing. IDE devices are slow compare to SATA ones. These storage devise comprise of head for read write, platters to store data, spindle motor to rotate platters, HAD and electronics board also called PCB. They are made dust proof and they used to be cheaper but now other types are taking over so the prices of these IO devices are going up.
IDE drives are outdated now. They had two drawbacks, first they were slow, and second their storage capability was not that big. SATA was the next one which pushed IDE to the background. SATA dominated the market for quite a few years; in fact they are still popular. The storage capacity was small just like IDE and went up from GB (Gigabyte) to several TB (terabyte). Because the majority of market share was with Microsoft which was being used in PCs and Laptops, A need for speed was felt according to my personal experiences and observation. Computer systems were getting slow because of modern applications and viruses, the need for speed was felt severely. This gave birth to the new type of hard disks called as solid state drive (also known as SSD). SSD is faster and getting cheaper. They come in just one size that is 2.5 inch. They are usable in desktops and laptop computers.
After regular 2.5” SSD drives, we were introduced with a small SSD called MSATA. It is a kind of mini pci express type. It is even faster than traditional SSD which communicates with a SATA connection. The mini PCI express was a fast bus structure. Both these SSD types were introduced in Microsoft and Linux based computer systems. Then Apple introduced en even faster SSD drives that were named as Apple PCIe drives. These look like a desktop ram but they are really fast and are being used in Apple Mac desktop computers and MacBook Pro. Because of speed and reliability, they are not that cheap compare to other SSD drives. SSD drives are made of nand chips, controller and PCB. They drives are supply light and supper shock proof because of no moving parts inside them.
After MSATA a new family of drives were introduced known as m.2 drives. M.2 uses PCI express lanes instead of SATA bus used in previous SATA SSD storage. The older SATA SSD were supper expensive and unreliable. These problems were solved in the new m.2 technology. M.2 were previously known as NGFF (Next Generation Form Factor). M.2 make use of PCI Express and many other buses. These drives mainly took place of mSATA and mini PCI Express. This technology is now being supported by Intel CPUs and many motherboard brands like MSI and ASUS. This technology was also used in wifi cards. There are mainly two types in the family. B+M key and M key. These devices come in different sizes like 2242, 2260, 2280 and 22110. The first two digits represent the width and the last 2 or 3 digits represent length of the drive. The bigger the length is , there are more chances, the larger will be the capacity. In spite of all this development these devices can fail. Mostly there is logical failure that can be painful but it is not that bad because data recovery is still possible just in case if there I important data on them.
In this article I spread light on different types of solid state hard drives. I talked about old SSDs and new SSDs demonstrating modern technological advancements.
If you are in a situation of recovering data from msata, m.2 ssd, nvme drive after a dead laptop or tablet like surface pro then contact our data recovery Mississauga lab. We have been successfully recovery these drives with the right equipment and experience.
How much data recovery cost?
In this article I will talk about how data recovery service is priced. I will also explain how different devices affect the price when it comes to rescuing important information. I will cover all the devices that may be involved in this process.
How much data recovery cost, is a huge question. It is not easy to answer this question without going into a lot more details. First of all I will differentiate data recovery from data transfer. Data recovery is a process in which important content is extracted from an electronic device or a storage media. Data transfer is a process in which information is moved from one device to the other without involving high end professional expertise and tools. This could be simply moving any kind of information from one working computer to another, one working hard drive to another, one working flash card to another, one working disk to another or one dead computer to an external hard drive assuming the hard drive is ok but the computer is dead. Cost for content transfer is usually low. Most places charge $1 per GB for data transfer. Some companies charge high and some charge low but the fair practice is, most would charge less for just a transfer.
So how is the recovery service priced? It’s an important question and it needs a really good explanation because we hear this question all the time. Price for data recovery depends on many factors. One example is whether it is a recovery or just a transfer. I have already put some light on data transfer cost in the above lines. One thing that I missed in the cost explanation was, if a computer or electronic device is dead, it’s fair to add a small fee for diagnosis of the device in addition to data transfer cost.
Professional data recovery is a process of retrieving files from all kinds of storage devices when data is inaccessible in a normal way. This could include PC desktop computer, laptop, server, mac, macbook, network attached storage, external and internal hard drive, usb flash drive, solid state drive, sd card, floppy and zip disk, hand held devices like ipad, iphone, android phone, video camera, digital camera, recording devices or any other kind of storage device. So question again is how much it will cost to recover files from a hard drive that is not showing up on a computer? It’s a tricky question. There might be multiple scenarios. Is it corrupt file system on the drive? Is mount partition missing from the drive? Is it an electronic issue that is stopping the drive from mounting? Is it software corruption inside the drive?
Is the surface that store all the files has issues? Is the read and write head weak or broken? Is the drive motor seized or malfunctioning? Has the drive slowed down? Is the drive having bad sectors? How much is the drive capacity? How long it will take to recover the drive? These are all the questions that are very crucial. These questions determine a direction for pricing. So this means, if there is a hardware issue with the drive, it must first be repaired or the part must be replaced in order perform a recovery. This changes the recovery process into advanced level of hard drive repair process. In this process, the drive is repaired by replacing defective parts and then professional tools are used to complete the complex part of the recovery.
This means, it is impossible to provide a quote without proper evaluation of a device. This is the reason why professional companies always offer free evaluation. Evaluation is a process in which a through investigation is performed to see what needs to be done and what approach will be taken to recover a drive. Many people compare data recovery with computer and laptop repair process. It has nothing to do with PC or Mac or any other device repair. This is a completely different process and must not be compared to normal computer or laptop repair. A wrong approach will definitely destroy the recovery chances.
In this article, I talked about different facts that help how data recovery price is determined. If you need someone with professional data recovery profile, please contact the following service.
Data Recovery Complications
In this article, I will talk about several difficulties ranging from basic to complicated ones that might make the data recovery impossible. I will also talk about the reasons of these complications.
We use data on hard drives and computer systems and are always worried about our data security. For the protection of our data, we mostly use passwords. There are various levels of securities when it comes to passwords. There are professional systems that use complex programs encrypting information. This kind of security is considered the highest one. The way normal user passwords were being used with traditional operating systems has changed over time. In older operating systems whether it was windows PC computers or Mac computers, the contents could be read offline even if there was a password on user account. Apple started high-end security allowing users to protect their information when it comes to accessing it off-line.
Talking of modern operating systems, I have to give credit to Apple who brought secure system known as File Vault. This is a built-in feature in their modern operating systems on all MacBook Pro, iMac, MacBook Air and all other Apple computers. Under this system, if it is turned on, the computer uses the user’s login password and encrypts the data. This is very good feature available in all new operating systems in all Macintosh computers, ipads and iPhones. Windows systems come with their own BitLocker feature that encrypts the data if the feature is turned on. Encryption is very high level system which is not easy to break without proper technology. Encrypted data or passwords are one level of difficulty in data retrieval. There is a second one which will be discussed in the following lines.
When a hard drive, usb, server drive or nas fails, we have to deal with the first line of security which is the password but what if the hard drive fails physically? This is the hard one. When a drive i.e. a traditional storage or flash drive physically fails, this can be a big problem. Password information is stored randomly all over the available space. If an area where the password or key information is stored is not accessible, it will be impossible to recover data even if we have the right password or encryption key. This means, if someone has encrypted password on storage and they format the drive, this will make data recovery impossible. On the other hand data recovery using the right tools and technology may be quite possible if the physically broken drive is properly recovered and then password is applied. A lot of time users try different software and follow online instructions to attempt a recovery. This approach brings the same destruction as if someone deletes or formats a drive that has a secure or encrypted data combined with a password.
There are a lot of online services and companies that claim that their data recovery software can recover any kind of situation. This is mostly not true. Trying different software, copying more content to the drive, running a physically damaged drive unnecessarily increases the high risk losing data permanently. It does not matter if the data is password protected with password or not trying different ways and letting other inexperienced technicians playing with these situations is not recommended ways for data recovery. When it comes to crucial data recovery, it is highly recommended to do a little research about data recovery otherwise risk of losing data will always remain high.
In this article, I talked about some important facts when it comes to data recovery from storage devices that are password protected and they have physically failed.
Macbook Pro Pros and Cons
Today in this article, I will talk about different kinds of known issues with Apple Macbook Pro laptops. I will also throw light on their top quality and reliability.
Macbook Pro is a super laptop introduced by Apple Company. This laptop is considered best for a few reasons. This machine is super power full. The operating system is very secure and full of innovations. This machine has many unbeatable features. The battery life is long. The quality and hardware is so good that most of the time it can survive liquid spill. The logicboard design is wonderful. We deal with this machine on a regular basis. The graphics processing is high class. The screen quality and resolution is at best. Other features include airplay, time machine backup, iTunes backup and more. The machine is physically strong. The body is beautiful. We highly recommend Apple’s MacBook Pro for personal as well as commercial use.
We have been dealing with this machine since Apple changed their processor from IBM to Intel. Apple introduced many machines since 2006. Their pro family included 15 and 17 inch pre-unibody Macbook Pro machines that they introduced from 2006 to 2008. They introduced 15 and 17 inch unibody Macbook pro laptops from 2009 to 2011. These machines worked great for years until they showed bad graphics symptoms. After many years of use, these machines’ graphics card failed due to a third party chip. These symptoms would include, black screen, rebooting, colored screen, grey screen, panic screen, colored lines and freezing issues. Apple had two recalls for these machines, last one finished in December of 2016. After the recall time was over, everybody was disappointed until we came with a permanent solution. We can fix problems in all the above and below models.
The new family which they introduced in mid 2012 was named Macbook Pro retina. They came in both 13 inch and 15 inch. The 15 inch from mid 2012 and early 2013 exhibited video problem due to a third party chip again. This is the most powerful machine. We invented a fix for this model too. We can fix it and the problem will never come back. The next family that has some known issue is the mid 2012. The machine will show a folder sign with a question mark inside the folder. This can be fixed by our Apple certified technicians. Some macbooks have another type of problem, where the machine starts with black screen. This is a random issue with 13 inch macbook pro. There is this other known issue where a 13 inch macbook pro from 2015 would have problem with keyboard and trackpad. All these problems are fixable by Apple and by us. Over all these issues are not found in every single machine but because Apple have sold many models to consumers, the high the number, the more we find problematic machines. Apple offers all kinds of repair options for their products. Their warranty service is very good. We also fix all Apple products.
In this article I talked about several models of Macbook Pro models and problems associated with some models.
Data Recovery Mistakes
In this article, I will talk about the dos and don’ts of data recovery. I will talk about how computer users try to destroy hard drives with to recover them themselves without proper arrangements.
Data recovery is the process of retrieving data from a failed storage or media. This could be any thing like physically defective drive, deleted media or corrupted hard drive. Different scenarios have different kinds of solutions. For example, for logical problems, specialized and appropriate software is used. For physical problems, the drive’s hardware is fixed or replaced. This cannot be easy for a normal user because they would have no idea what to use in particular situation. We have seen people literally destroying drives and making data recovery impossible. This practice is becoming common due to You Tube videos. There are so many people on You Tube who will try these things without knowing the fact that many people might follow them in doing so.
In what circumstances users should try recovery attempts? This is a crucial question. The simple answer is, if the data is important, no self recovery attempt is recommended. There are many reasons for that. Let’s say it is a logical situation where the data was lost as a result of accidental deletion, software corruption, or format, still there are huge chances of recovery if certain steps are not taken. The most important one is using the devices after the event or accident. If the above happens, it is strongly recommended to stop using the device and the device be taken to a professional computer data recovery lab. The reason behind is, if the device is in use, data will be read and written to it without user’s knowledge because there might be many apps that would receive and send data, phone calls logs and so on. The next reason is, if data recovery is needed, it is dangerous to install data recovery software on the device or media. People often install data recovery software on c drive, iPhone, iPad or other phones and destroys the free space where the deleted data might be stored. Deleted data is always stored in empty space. There are many data recovery software available on the internet and very company claims that their tool is the best but the fact is opposite of the situation. Most of these companies don’t even warn the users not to install the software on the affected device. These are the reasons why data recovery should not be tried without experience. It does not matter it is flash memory or traditional drives; it is equally destructive for all media. So it is highly recommended not to try the above if the data is important.
Let’s see what is going on with failed drives. Traditional hard drives have moving parts inside. If they physically fail, there might be a few reasons like bad electronics, bad motor, defective heads, damaged platters. Physically failed drives mostly make noises. This leads users to search to fix them by themselves. They go online and look for videos and tutorials how to fix the drive’s internal problem. This is where the situation goes out of control when they open these drives and play around with them. These drives are factory sealed to stop dust getting inside the drive. In order to open these drives, a dust free environment is a must. If the drive is opened without proper clean environment, the platters and heads would collect enough dust to destroy the surface especially if the drive is run after opening it. This is the most unwanted work that we have seen with many people. This is happening because of lake of information by these online users who would not warn users not to try it at home etc. It is therefore advised not to copy online videos and instructions to open a drive if the data is important.
In this article, I put light on what not to do when data storage media has failed logically or physically.
Hard drive and data recovery
In this article, I will talk about all kinds hard drives, how they work and what can be done when they fail. I will also talk about the data recovery process.
There are many kinds of hard drives like regular hard drive used in desktop computers, small drives used in laptops, portable external hard drives that are used for data storage. All new computers mostly come with a new family of hard drives known as solid state drives. Hard drives come in different sizes and capacities. Some come in 3.5 and others 2.5 inches. Hard drives also come with different read and write speeds. Regular drives use traditional medium and techniques and that is why the read and write speeds are slower than modern flash drives. The read and write operation in traditional drives is done by heads. These heads move back and forth on platters in order to read data and write data. The reading and writing speeds varies depending on surface condition on the platters. When heads move, they make noise while solid state drives don’t make noise because there are no moving parts. When heads fail in traditional drives, data becomes inaccessible. Similarly when controller in solid state drives fails, data read and write operation stops. In solid state drives, data is stored in multiple chips while in traditional drives, data is stored on the surface of platters in a specific way. All external hard drives or storage systems have regular or flash drives inside enclosures.
Traditional drives have electronics board called PCB. The board controls input power to the drive. There is one connection for heads and one for motor via pcb. The motor is responsible for rotating platters. The drive can have multiple platters. The bigger the capacity is, the higher will be the number of platters. The same is for the number of heads. If there are more platters, there will be more heads. Usually every platter has two read write heads. One is responsible to read and write the top surface and the other reads the bottom side of the platter. Traditional hard drives work with the help of some important program stored either in a chip on the PCB or on platters. In case of solid state drives, the controller has all controlling modules mostly but some hard drives have these modules in data chips too. Flash drives known as SSD have multiple chips for storing data. The bigger the capacity, the higher is the number of chips to store larger amount of data. Traditional hard drives have different read and write speeds. Some have 5400 and others have 7200 rpm or more. Some are used for data store like network drive, others are used for operating systems processing. Solid state drive have high read and write speeds.
There are is another family of storage devices that are not like hard drives but they are known as flash cards or flash drives. They mostly come in two types, sd memory cards and usb flash drives. SD cards come in different sizes and capacities. The smaller ones are known as Micro SD cards. The regular cards have a plastic housing, a small board, controller and nand chip. Nand chip stores data; controller has the functions of controlling operations while the board acts like a mother for putting everything together.
There are many companies that make these drives. A few to name are Western Digital, Seagate, Hitachi, Toshiba, Maxtor and others. These companies have been making traditional drives in the past but now they started making SSD storage too. Some other companies that make SSD drives are Samsung, Adata, T5, Intel etc. Traditional hard drives are becoming less popular due to high popularity of SSDs. The reason is, they are fast and shock proof although they can also fail. Some time ago, flash drives were very pricy but now the prices have dropped. These drives are fast and if their price goes down more and more people will start using them. There are many kinds of drives in both traditional and flash. In traditional there are 1.7 inch, 2.5 inch and 3.5 inch drives. In flash, there are regular 2.5 inch, msata, pcie and m.2 ssd drives. When it comes to weight, traditional 3.5 inch and even 2.5 inch drives are heavier than flash drives. Whether it is traditional or SSD, they can fail. The failure can be of different nature.
When a hard drive fails, the process that can bring the data back is known as data recovery. There are many types of failures when it comes to hard drives. There might be software corruption, operating system failure, files may have been deleted or drive might have been formatted accidentally. Other problems include power issue, liquid damage, fire or other physical problems. In SSDs controller failure, chip failure, board failure or software corruption in controller might be the possible reasons for failure. If it is a software issue then different software tools can be used to recover data but which tool is right, it is not easy to guess. There are hundreds of data recovery software available by different sellers and manufacturers. They all claim that their software will recover any situation but the fact is against it. Only few works but it all depends on what we know about specific software. Most of the seller will offer a free trail for downloading. After running, files will be shown with thumbnails or names. This is usually enough for a user to believe that the software is good but again the fact is against it. Once the user buy the software and run the scan with fully functional version the results will be different. The files will not fully open in regular size but thumbnails will be shown which is not acceptable to users. They will be rather small icons. This is very common practice these days. Therefore it is very important to know that trying different trials software is not a good way to start with and this may a permanent data loss if data is overwritten.
If a drive has data and has hardware failure, the job becomes more sensitive. The best way to deal with this kind of situation is to take the drive to a professional data recovery company. This kind of recovery may involve all sort of hardware repairs like PCB repair, head repairs or replacement, firmware repair etc. This kind of work needs experience, techniques and professional technology. It is highly recommended not to open the drive without clean environment and YouTube videos must be avoided if data is important. The reason is these videos do not show all warnings and side effects. The possible repairs in case of physical failure of a drive are replacing parts like board, heads or motor. Head replacement is a complex procedure. Certain rules must be followed to swap heads otherwise chances are data will be lost forever.
This article was about general knowledge about hard drives and data recovery. If you need expert and professional data recovery services for all kinds of drive failure situation, we are here to help. Contact us for more details.